Exam Code: 156-215.81
Exam Name: Check Point Certified Security Administrator R81
Certification Provider: Checkpoint
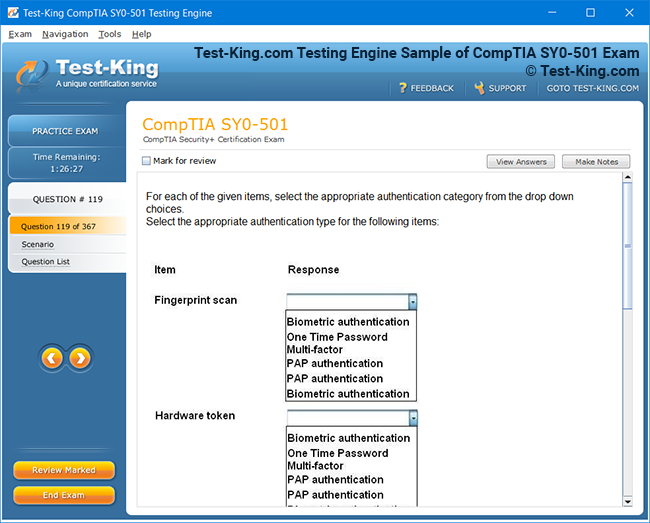
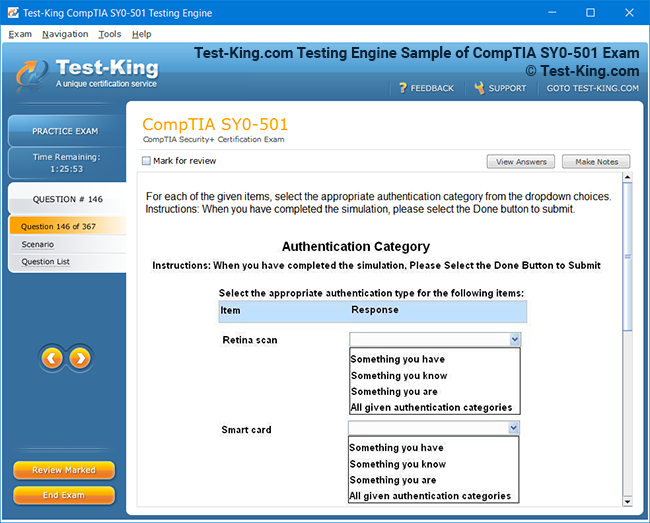
Product Screenshots
Frequently Asked Questions
How can I get the products after purchase?
All products are available for download immediately from your Member's Area. Once you have made the payment, you will be transferred to Member's Area where you can login and download the products you have purchased to your computer.
How long can I use my product? Will it be valid forever?
Test-King products have a validity of 90 days from the date of purchase. This means that any updates to the products, including but not limited to new questions, or updates and changes by our editing team, will be automatically downloaded on to computer to make sure that you get latest exam prep materials during those 90 days.
Can I renew my product if when it's expired?
Yes, when the 90 days of your product validity are over, you have the option of renewing your expired products with a 30% discount. This can be done in your Member's Area.
Please note that you will not be able to use the product after it has expired if you don't renew it.
How often are the questions updated?
We always try to provide the latest pool of questions, Updates in the questions depend on the changes in actual pool of questions by different vendors. As soon as we know about the change in the exam question pool we try our best to update the products as fast as possible.
How many computers I can download Test-King software on?
You can download the Test-King products on the maximum number of 2 (two) computers or devices. If you need to use the software on more than two machines, you can purchase this option separately. Please email support@test-king.com if you need to use more than 5 (five) computers.
What is a PDF Version?
PDF Version is a pdf document of Questions & Answers product. The document file has standart .pdf format, which can be easily read by any pdf reader application like Adobe Acrobat Reader, Foxit Reader, OpenOffice, Google Docs and many others.
Can I purchase PDF Version without the Testing Engine?
PDF Version cannot be purchased separately. It is only available as an add-on to main Question & Answer Testing Engine product.
What operating systems are supported by your Testing Engine software?
Our testing engine is supported by Windows. Andriod and IOS software is currently under development.
Top Checkpoint Exams
- 156-315.82 - Check Point Certified Security Expert - R82 (CCSE)
- 156-215.82 - Check Point Certified Security Administrator R82
- 156-215.81.20 - Check Point Certified Security Administrator - R81.20 (CCSA)
- 156-315.81.20 - Check Point Certified Security Expert - R81.20
- 156-587 - Check Point Certified Troubleshooting Expert - R81.20 (CCTE)
- 156-536 - Check Point Certified Harmony Endpoint Specialist - R81.20 (CCES)
- 156-582 - Check Point Certified Troubleshooting Administrator - R81.20 (CCTA)
- 156-835 - Check Point Certified Maestro Expert
- 156-560 - Check Point Certified Cloud Specialist (CCCS)
- 156-585 - Check Point Certified Troubleshooting Expert
The Foundations of Check Point Certification and Why 156-215.81 Matters
In the dynamic field of cybersecurity, certifications play a crucial role in validating the expertise of IT professionals. Check Point, a leading security solutions provider, offers certifications that focus on safeguarding networks, managing firewalls, and implementing threat prevention strategies. Understanding the importance of certifications like 156-215.81 allows professionals to establish credibility and demonstrate practical proficiency in securing organizational systems. While knowledge of general networking concepts is essential, grasping platform-specific technologies enhances a candidate’s ability to protect sensitive data.
This foundational knowledge not only improves individual competency but also strengthens the security posture of organizations. Professionals who combine certification with hands-on experience can anticipate potential vulnerabilities, respond to incidents more efficiently, and contribute to the development of security policies that are both practical and compliant with industry standards. Building such expertise sets the stage for advanced learning and prepares candidates for real-world security challenges, ensuring their skills remain relevant in a rapidly evolving landscape.
The Importance of Networking Fundamentals
Before diving into Check Point-specific concepts, having a solid foundation in networking is critical. Cisco IOS, for instance, is the backbone of many enterprise networks, providing the command-line interface and modular architecture required for network configuration and management. Professionals must understand Cisco IOS step by step to gain insights into routing, switching, and policy enforcement, which complement the security expertise expected from Check Point certifications. Such knowledge ensures seamless integration between security and network operations.
Networking fundamentals allow security professionals to troubleshoot issues effectively and optimize performance across complex infrastructures. They also enable administrators to understand how policies and firewall rules affect traffic flow, which is essential when implementing security measures that do not disrupt normal operations. By mastering these basics, candidates gain a holistic view of network behavior, improving their capacity to design secure and efficient architectures that support both internal and external communications in enterprise environments.
Exploring the Digital Infrastructure
Modern IT environments are built upon complex ecosystems where network devices, cloud services, and security platforms intersect. Understanding Cisco’s tech ecosystem provides valuable context for Check Point administrators. Knowing how different components interact allows professionals to design secure, scalable, and resilient networks. Security decisions, such as deploying firewalls or VPNs, are more effective when aligned with the underlying infrastructure’s architecture, which is often a blend of physical and cloud-based solutions.
This awareness helps professionals anticipate integration challenges and identify potential points of failure. By analyzing how systems communicate and where sensitive data resides, security administrators can implement layered defenses, such as intrusion prevention systems, endpoint security, and segmentation strategies. Understanding the ecosystem also facilitates collaboration with other IT teams, ensuring that security solutions complement network operations, storage strategies, and cloud adoption plans without introducing bottlenecks or conflicts.
The Evolution of Certification Paths
The cybersecurity certification landscape is continuously evolving to reflect emerging threats and technological advancements. Cisco’s upcoming 2025 certification path illustrates how vendor certifications adapt to new standards. Similarly, Check Point updates its exams to incorporate the latest features in its R81 platform, ensuring that certified professionals remain current. Staying aware of these changes helps IT professionals align their learning strategies with industry trends and maintain relevance in competitive job markets.
Remaining current with certification paths provides a roadmap for continuous professional growth. It allows candidates to prioritize learning objectives, focus on high-demand skills, and strategically plan recertification. Additionally, understanding evolving certification standards enables professionals to benchmark their expertise against industry expectations, giving employers confidence in their ability to manage modern network environments effectively while maintaining robust security practices.
From Beginner to Expert
A structured learning pathway is essential for mastering any technology. Following a clear certification pathway equips professionals with foundational skills before progressing to advanced expertise. For Check Point, this progression might start with entry-level courses on firewall basics, advancing to complex threat prevention and security management. Understanding each stage allows candidates to build confidence while systematically acquiring knowledge, ultimately preparing them for demanding exams like 156-215.81.
Structured learning reduces the risk of knowledge gaps and ensures that professionals can handle increasingly complex scenarios. It encourages a disciplined approach to mastering configuration, troubleshooting, and monitoring tasks. Moreover, by gradually advancing through beginner, intermediate, and expert stages, candidates cultivate both theoretical understanding and practical competence, improving their ability to implement secure network architectures effectively.
Integrating Cloud Security Knowledge
Security in cloud environments has become a critical competency for network administrators. The rise of cloud platforms like AWS necessitates understanding how services operate and how security measures integrate with these systems. The AWS Machine Learning specialty exam provides insight into protecting data in cloud-based workflows, reinforcing the need for cybersecurity professionals to extend their expertise beyond traditional network boundaries. Such interdisciplinary knowledge improves the ability to implement comprehensive security strategies.
By combining cloud security knowledge with firewall management, administrators can ensure consistent protection across both on-premises and cloud infrastructure. This integration allows for centralized monitoring, automated threat detection, and dynamic policy enforcement. Furthermore, understanding cloud platforms’ security models helps professionals assess risks, configure compliance controls, and respond quickly to potential incidents, significantly enhancing overall organizational resilience.
Comparing Cloud Providers
When designing secure networks, professionals must also evaluate competing cloud providers to understand potential risks and deployment strategies. The Amazon vs Alibaba market growth comparison highlights differing approaches to scalability, infrastructure, and security controls. This awareness enables IT administrators to tailor Check Point solutions for hybrid or multi-cloud environments, ensuring consistent protection across platforms and aligning security policies with the organization’s strategic cloud objectives.
Analyzing multiple cloud providers allows professionals to make informed decisions about workload placement, redundancy, and data sovereignty. By understanding each provider’s strengths and limitations, security policies can be optimized to reduce exposure to vulnerabilities while maintaining performance standards. This strategic approach ensures that the organization’s security posture remains robust, even as workloads shift between different cloud infrastructures.
Understanding Market Leadership
AWS has emerged as a dominant force in cloud services, offering reliable platforms for businesses to host applications and data. Learning from industry leaders, such as in the key reasons AWS led, helps security professionals anticipate challenges and leverage best practices. Check Point certifications, including R81-focused exams, integrate principles of network protection, cloud integration, and automated threat detection, providing professionals with the tools to maintain security leadership in any digital infrastructure.
Studying market leaders also inspires professionals to adopt innovative security measures and automate routine tasks. By following proven strategies, administrators can implement scalable defenses, reduce human error, and focus on strategic security initiatives. This proactive approach ensures that network defenses remain adaptive and resilient against evolving cyber threats while aligning with organizational growth objectives.
Data Management and Warehousing
Effective security strategies often rely on robust data management. Amazon Redshift offers a prime example of how structured data storage and retrieval support analytics and security monitoring. Professionals familiar with data warehousing with Redshift understand how to secure databases, implement access controls, and monitor suspicious activity. Such knowledge complements firewall management and threat prevention capabilities, enhancing the practical skill set required for Check Point R81 certification.
Secure data management also enables administrators to maintain compliance with regulatory standards, detect anomalies proactively, and perform forensic investigations when incidents occur. By implementing effective monitoring, encryption, and auditing practices, professionals reduce the risk of data breaches while providing accurate reporting for stakeholders. Integrating these strategies with firewall and network security strengthens the organization’s overall defense mechanisms.
Building Cloud Competence
For aspiring security experts, foundational cloud knowledge is vital. The AWS Cloud Practitioner prep course provides a structured introduction to cloud security concepts, helping candidates integrate these principles with Check Point technologies. By understanding how to manage identity, access, and network segmentation in cloud environments, professionals can design more resilient security frameworks that align with both on-premises and cloud systems.
Developing cloud competence allows professionals to address hybrid architectures confidently, optimize resource allocation, and implement consistent security policies across environments. It also equips administrators to troubleshoot incidents effectively, automate compliance reporting, and leverage cloud-native tools to strengthen defenses. This holistic understanding ensures that certified professionals are capable of supporting modern, dynamic IT ecosystems with a high level of security assurance.
Specialty Skills and Advanced Exams
Advanced cybersecurity roles increasingly require expertise in niche areas, such as machine learning for threat detection. The AWS Machine Learning quick reference highlights the application of predictive analytics in identifying malicious activity. Check Point administrators with knowledge in such specialties can extend the capabilities of R81 systems, implementing proactive threat prevention strategies and optimizing network security through intelligent automation and continuous monitoring.
Specialized skills allow professionals to anticipate threats, respond faster to incidents, and implement adaptive security controls. Combining machine learning with Check Point R81 technologies can enhance anomaly detection, identify suspicious patterns, and improve the overall effectiveness of security operations. By embracing these advanced skills, IT professionals position themselves as strategic assets, capable of driving both innovation and robust defense strategies in complex digital infrastructures.
Advanced Concepts in Check Point R81 Security
Mastering Check Point R81 requires a thorough understanding of advanced network security concepts, starting with how data structures and programming logic can influence security automation. Many administrators use scripts to manage repetitive tasks and monitor traffic logs efficiently. For instance, understanding how to count occurrences of specific events in logs can aid in detecting anomalies or repeated intrusion attempts, making it essential to know methods like counting occurrences of items in a Python list to streamline analysis.
Automating these tasks reduces the risk of human error and improves response times. By tracking repeated patterns or irregular activities programmatically, security teams can prioritize incidents and allocate resources effectively. Python scripting becomes a core skill, allowing administrators to integrate custom monitoring tools with Check Point dashboards, further enhancing situational awareness and operational efficiency across the network.
Optimizing Security with Digital Visibility
Visibility into traffic patterns and system activity is critical for proactive security. Administrators increasingly rely on digital marketing principles and online strategies to understand attack vectors, similar to how content creators analyze reach using YouTube SEO ranking tips. In cybersecurity, analyzing access patterns, frequency of connections, and unusual requests provides a comparable insight, allowing security teams to optimize firewall rules and preemptively mitigate potential threats.
Understanding traffic trends allows administrators to adjust policies to balance security with performance. Just as SEO techniques ensure content reaches the right audience, targeted network monitoring ensures legitimate traffic flows smoothly while suspicious activity is flagged. This approach supports continuous improvement in security policy enforcement and operational efficiency.
Fundamentals of Blockchain Security
The growing adoption of blockchain technologies has influenced network security considerations. Professionals exploring decentralized finance or cryptocurrency must grasp mining principles, including verification and consensus mechanisms, to safeguard transactions. Knowledge gained from beginner’s guide to Bitcoin mining aids security experts in evaluating risks associated with digital currencies, wallet security, and transaction validation within organizational networks.
Integrating blockchain awareness into network security strategies strengthens overall resilience. Administrators can identify potential vulnerabilities, implement secure nodes, and design systems that prevent unauthorized access. By understanding the underlying protocols, security teams enhance their ability to protect both financial assets and critical network infrastructure from sophisticated attacks.
Efficient Data Handling in Programming
Check Point administrators often use programming techniques to enhance the effectiveness of firewall rules and logging scripts. Being able to locate and manipulate specific data within a container is vital for automation and threat detection. Concepts similar to finding elements in C++ containers using iterators enable administrators to efficiently search for anomalies or policy violations within large datasets, improving operational workflow.
Efficient data handling ensures that alerts and system reports are accurate and actionable. By leveraging iterators or similar programming constructs, administrators can monitor specific traffic types, validate security policies, and maintain compliance with organizational standards. This precision reduces false positives and allows for more targeted interventions in network management.
Handling Text and Case Sensitivity
Security logs often contain entries with varying capitalization, which can affect automated monitoring scripts. Understanding how to normalize data is crucial for accurate reporting and analysis. Learning how to convert text to lowercase, as shown in convert string to lowercase in Python, ensures consistency in data handling and prevents misinterpretation of repeated or suspicious events.
Normalization reduces errors in automated alerts, simplifies comparisons, and enables more reliable trend analysis. By standardizing log data, security teams can apply consistent filtering and pattern recognition methods, making anomaly detection more accurate and ensuring that important events are not overlooked in routine monitoring tasks.
Preparing for Advanced Certifications
Check Point experts often pursue certifications to validate their knowledge and enhance career prospects. Preparing for exams like Microsoft’s DP-100 provides insights into data handling, analytics, and threat detection. The DP-100 exam difficulty and preparation tips serve as a model for structured study approaches, emphasizing the importance of hands-on practice, understanding exam objectives, and managing time effectively during testing.
Structured exam preparation reinforces practical skills and ensures professionals can demonstrate competency in high-stakes environments. This disciplined approach translates to operational excellence in daily tasks, allowing security teams to confidently implement and manage advanced firewall policies, intrusion prevention measures, and threat analysis procedures.
Comparing Cloud Security Solutions
Understanding the differences between monitoring tools and security management platforms is vital for Check Point administrators managing hybrid or cloud environments. Knowledge of platforms like Azure, including Azure Sentinel versus Azure Security Center, helps professionals determine which tools are best suited for automated detection, alerting, and incident response, ensuring comprehensive coverage across distributed systems.
Selecting the appropriate platform ensures efficient threat detection and response while minimizing administrative overhead. Security teams can integrate Check Point systems with cloud-native monitoring, leveraging automation and analytics to proactively address potential vulnerabilities and maintain continuous compliance with organizational policies and regulatory requirements.
Advanced Cloud Administration
Cloud-focused exams like DP-200 provide a framework for understanding data deployment, integration, and management in cloud environments. Preparing using Microsoft Azure DP-200 strategies equips professionals with skills to implement robust security measures, configure high-availability setups, and optimize performance across virtual networks, complementing Check Point firewall expertise.
This knowledge supports secure data flow, ensures compliance, and enables rapid response to incidents. By mastering cloud administration concepts alongside Check Point tools, professionals can maintain unified security strategies, automate monitoring, and enhance the resilience of enterprise systems against evolving cyber threats.
Building a Strong Azure Foundation
Understanding cloud fundamentals is essential before tackling advanced security configurations. Resources like Azure Fundamentals exam guide provide a clear overview of cloud services, identity management, and governance. This foundation allows administrators to implement secure, scalable policies in Azure environments while integrating Check Point solutions for comprehensive threat prevention.
Foundational cloud knowledge helps ensure that security policies are correctly aligned with operational requirements. It enables administrators to anticipate configuration issues, implement best practices, and optimize network segmentation for both on-premises and cloud resources, contributing to more resilient and manageable infrastructures.
Enhancing Database Security Skills
Database security is a critical aspect of network defense, and SQL remains a core tool for querying, monitoring, and reporting on data activity. Mastering key SQL techniques, as highlighted in top 100 SQL interview questions, helps security professionals efficiently retrieve, analyze, and protect sensitive information stored in enterprise databases, supporting comprehensive threat detection and auditing.
SQL expertise allows administrators to detect unauthorized access, enforce data policies, and monitor trends that could indicate potential breaches. Combining these database skills with firewall and cloud security capabilities enhances overall defense, ensuring that data integrity and confidentiality are maintained throughout the organization.
Advanced Database Management for Security Experts
Database management is not just about storing and retrieving information; it is also about ensuring that the right data is accessible securely when it is needed. Effective management involves designing structures that support rapid queries, maintain integrity, and safeguard sensitive information against potential breaches. Security experts must balance accessibility with protection, ensuring that only authorized users and processes can interact with critical systems. Check Point R81 administrators often rely on database insights to monitor traffic logs and identify abnormal activity, which is crucial for maintaining network security.
Managing complex databases is a critical aspect of cybersecurity, particularly when working with Check Point R81 firewalls that rely on structured data for logs, policies, and alerts. Professionals seeking to deepen their expertise often pursue certifications like the AWS Certified Database Specialty, which demonstrates proficiency in designing, deploying, and securing database solutions in cloud environments. Understanding database fundamentals helps administrators efficiently analyze logs, detect anomalies, and manage threat intelligence data.
Effective database management ensures that security events are logged accurately and can be retrieved quickly for analysis. Structured queries and optimized storage reduce latency in retrieving critical information, which is essential during incident response. By integrating database expertise with firewall management, professionals can enhance automated monitoring and implement predictive threat detection strategies.
Cloud-Based Application Security
Cloud application development requires an understanding of both software architecture and underlying infrastructure. Applications in cloud environments often interact with multiple services, which makes secure integration essential to prevent unauthorized access and data leakage. Administrators must account for identity management, encryption, and API security while ensuring performance is not compromised. By learning from cloud-focused certification programs, professionals can design resilient applications that work harmoniously with network security protocols.
Developing secure applications in cloud environments requires knowledge of both programming and cloud infrastructure. Certifications like the AWS Developer Associate guide professionals through creating, testing, and securing applications using best practices. Applying these concepts alongside Check Point R81 security policies allows administrators to protect endpoints and API interactions effectively, ensuring that applications maintain integrity under various threat scenarios.
Securing applications in the cloud also requires understanding permissions, identity management, and encryption. Developers and security teams must collaborate to enforce access policies, detect unauthorized attempts, and audit transactions regularly. This integration strengthens the organization’s overall security posture by ensuring that vulnerabilities in software do not compromise network defenses.
Enterprise Architecture and Security Frameworks
Enterprise architecture provides a structured blueprint that guides how IT resources align with organizational objectives. Understanding these frameworks allows administrators to integrate security consistently across systems, ensuring that firewalls, endpoints, and cloud services operate under unified policies. By adhering to proven methodologies, professionals can anticipate potential risks, improve incident response, and support compliance initiatives effectively.
Designing robust enterprise architectures involves aligning IT resources with security standards and organizational goals. Professionals often reference frameworks provided by organizations like The Open Group, which offer structured guidelines for implementing enterprise security, data management, and process governance. These frameworks complement Check Point certification training by providing a broader perspective on securing interconnected systems and maintaining compliance across large-scale infrastructures.
Applying enterprise frameworks helps administrators anticipate potential gaps in security coverage. Structured architectural designs ensure consistent deployment of firewalls, monitoring tools, and access controls, reducing the likelihood of breaches and improving the efficiency of incident response strategies across the organization.
E-Commerce Platform Security
E-commerce platforms are frequent targets for cybercriminals due to the valuable data they handle. Securing these platforms requires knowledge of payment protocols, user authentication, and vulnerability management. Professionals must ensure that sensitive information, such as payment details and customer credentials, is always protected through encryption, monitoring, and compliance with industry standards.
Securing e-commerce platforms requires specialized knowledge to prevent data breaches, protect customer information, and maintain transaction integrity. Skills obtained from Magento Developer certification help security professionals understand application-level vulnerabilities, implement secure payment systems, and integrate firewall rules that safeguard sensitive data. Combining application-level security with Check Point R81 firewall configurations ensures a multi-layered defense strategy.
Preventing security incidents in e-commerce environments is crucial for maintaining customer trust and meeting regulatory requirements. Professionals skilled in platform security can implement encryption protocols, monitor for suspicious activity, and create alerting mechanisms to respond quickly to potential threats, minimizing both financial and reputational risks.
Expert-Level Threat Management
Managing complex threats requires expertise beyond basic configuration. Administrators must anticipate attack patterns, understand advanced intrusion techniques, and deploy proactive measures that mitigate risks before they escalate. Expert-level proficiency involves continuous learning and practical experience in monitoring evolving attack vectors and adjusting defenses accordingly.
Achieving mastery in threat management involves in-depth understanding of both preventive measures and active monitoring techniques. The Certified Expert credential emphasizes advanced strategies for identifying vulnerabilities, managing security policies, and deploying proactive threat mitigation tools. When combined with Check Point R81 capabilities, this expertise allows administrators to implement sophisticated firewall rules and intrusion prevention strategies.
Expert-level knowledge enhances the organization’s ability to anticipate complex attacks, conduct thorough investigations, and deploy countermeasures before incidents escalate. Professionals at this level also mentor junior staff, ensuring knowledge transfer and consistent application of security standards across teams.
Endpoint Protection Management
Endpoints are increasingly the first targets in cyberattacks, making their protection essential. Security administrators must implement policies that enforce patching, malware prevention, and secure access while monitoring devices continuously for unusual behavior. Effective endpoint management prevents attackers from exploiting vulnerabilities to access sensitive systems.
Managing endpoint security is a critical responsibility for IT administrators, ensuring that all devices accessing the network are protected from malware and unauthorized access. The CMSS ePO certification focuses on endpoint protection platforms and management solutions, enabling professionals to configure antivirus, firewall, and patching policies that work in tandem with network-level controls provided by Check Point R81.
Strong endpoint management reduces the attack surface by preventing malware from reaching core systems. Automated patching, monitoring, and response capabilities allow administrators to enforce consistent security policies, maintain compliance, and quickly respond to threats detected on individual devices.
Network Security Policy Implementation
Policy creation is a balance between security and accessibility. Administrators must design rules that protect sensitive assets without hindering normal operations. Evaluating traffic flow, access needs, and compliance requirements ensures that policies are both effective and sustainable over time.
Developing and enforcing security policies at the network level requires knowledge of both configuration and compliance standards. Certifications like CMSS NSP provide guidance on designing policy rules, monitoring network behavior, and responding to violations. Implementing these principles in Check Point R81 ensures that traffic flows are controlled, threats are mitigated, and sensitive data remains protected across all network segments.
Effective policy implementation supports operational efficiency while maintaining strict security standards. Administrators can create layered defense strategies that combine firewall, VPN, and intrusion prevention configurations, ensuring that both internal and external threats are mitigated effectively.
Security Information and Event Management
Analyzing logs and alerts from multiple sources is complex, yet critical for proactive security. SIEM platforms help correlate events, identify anomalies, and automate responses. Professionals skilled in these systems enhance their organization’s ability to detect and respond to threats in real-time.
Monitoring, analyzing, and responding to security events is fundamental for any organization. The ISCPS SIEM certification provides expertise in using SIEM tools to aggregate logs, detect anomalies, and trigger alerts for potential security breaches. Integrating SIEM with Check Point R81 firewalls enhances the visibility of threats and allows administrators to respond proactively to suspicious activity.
SIEM solutions provide real-time insights and historical analysis, enabling organizations to identify patterns, investigate incidents, and enforce security policies consistently. Administrators skilled in SIEM enhance operational efficiency and reduce response times, minimizing potential damages from security breaches.
Microsoft Infrastructure Security
Securing server infrastructure is foundational for organizational cybersecurity. Professionals must manage permissions, updates, and monitoring while ensuring systems remain available and resilient. Understanding server configurations in depth reduces vulnerability to common attack vectors and supports compliance requirements.
Securing Windows-based networks is a common requirement for enterprise environments. Achieving the MCSA certification demonstrates proficiency in configuring, managing, and securing Microsoft server environments. By combining this expertise with Check Point firewall management, administrators can implement comprehensive protection strategies that address both network and server-level vulnerabilities.
Integration of network and server security ensures that access controls, authentication, and monitoring systems work cohesively. This layered approach reduces attack vectors, enhances threat detection, and maintains compliance with organizational and regulatory standards.
Cloud Productivity Security
Cloud collaboration platforms require unique security approaches due to shared access and distributed data. Administrators must configure identity and access controls, monitor usage, and enforce compliance while supporting team productivity. Effective cloud security allows organizations to leverage modern tools without introducing unnecessary risks.
Protecting cloud-based productivity tools and services is increasingly critical as organizations adopt Microsoft 365 solutions. The Microsoft 365 Fundamentals certification equips professionals with knowledge of identity management, compliance, and secure collaboration practices. When aligned with Check Point R81 network controls, administrators can enforce security policies that safeguard user data across cloud applications and services.
Securing cloud productivity platforms minimizes data leaks, prevents unauthorized access, and maintains organizational workflow continuity. Professionals who integrate cloud security best practices with traditional firewall protections create robust, adaptable security frameworks suitable for hybrid environments.
Continuous Improvement in Security Operations
Staying ahead of emerging threats requires ongoing education, collaboration, and practical experience. Security teams must adapt to evolving attack methods, update tools, and refine strategies regularly. Professionals who embrace continuous improvement can reduce exposure and maintain organizational resilience.
Mastery of multiple security disciplines enhances the capability to maintain resilient and adaptive networks. Combining database management, application security, enterprise frameworks, endpoint protection, SIEM expertise, and cloud knowledge allows Check Point R81 administrators to respond effectively to evolving cyber threats. Structured learning and certification achievements serve as benchmarks for operational excellence and strategic security planning.
Continuous improvement ensures that networks are prepared for emerging vulnerabilities, regulatory changes, and advanced attack techniques. Professionals who integrate cross-disciplinary knowledge improve overall incident response, optimize security policy enforcement, and contribute to the long-term resilience of their organizations’ digital infrastructure.
Fortinet NSE7 PBC Certification Overview
Network security requires a strong foundation in protecting perimeter and branch connections. Understanding secure communication protocols, VPNs, and firewall rules is essential for preventing unauthorized access. Professionals preparing for the NSE7 PBC 7.2 exam gain insights into the design and implementation of advanced firewall policies, which is critical for administrators managing Check Point R81 systems in enterprise environments.
This knowledge allows security teams to configure policies that safeguard sensitive traffic while maintaining operational efficiency. By understanding the principles of secure branch connectivity, administrators can minimize risk exposure, ensure compliance, and provide secure access to remote offices without compromising the overall security posture of the organization.
Fortinet NSE7 SD-WAN Implementation
Software-defined wide area networks (SD-WAN) have become a strategic tool for optimizing enterprise connectivity. Administrators must understand routing policies, traffic shaping, and security integration. Preparing for NSE7 SD-WAN 6.4 provides professionals with guidance on configuring and monitoring SD-WAN deployments, complementing firewall management skills for Check Point R81 environments.
Implementing SD-WAN effectively ensures reliable performance for critical applications, reduces latency, and enhances security. Network teams can enforce consistent security policies across multiple sites, leveraging SD-WAN intelligence to identify anomalous traffic, prioritize mission-critical applications, and maintain optimal connectivity without sacrificing safety.
Advanced Fortinet SD-WAN Skills
As enterprises scale, administrators must manage more complex SD-WAN configurations. Knowledge of traffic segmentation, application identification, and load balancing is vital. Certifications like NSE7 SD-WAN 7.0 focus on these advanced deployment scenarios, enabling professionals to integrate SD-WAN solutions seamlessly with existing network and security infrastructure.
Advanced SD-WAN skills allow organizations to dynamically route traffic based on performance metrics and security requirements. By combining these capabilities with Check Point R81 firewall rules, administrators can maintain high network performance while ensuring that all traffic is appropriately monitored, filtered, and protected from potential threats.
Fortinet SD-WAN 7.2 Enhancements
The latest SD-WAN updates include improved monitoring, automation, and security integration. Administrators must understand these enhancements to leverage full platform capabilities. Preparing for NSE7 SD-WAN 7.2 certification ensures professionals are equipped to configure optimized, secure networks that align with business needs and regulatory requirements.
Adopting these latest features allows organizations to respond proactively to network anomalies, optimize bandwidth utilization, and enforce consistent security policies across sites. Professionals who master these enhancements gain a competitive advantage, improving both operational efficiency and resilience against cyber threats.
Zero Trust Architecture Fundamentals
Zero Trust security principles demand that administrators verify every user and device before granting access. Integrating Zero Trust with firewall and endpoint policies enhances overall protection. The NSE7 ZTA 7.2 exam covers identity verification, access control, and continuous monitoring practices critical for implementing this model in modern enterprises.
Applying Zero Trust principles reduces the risk of lateral movement in case of a breach. Administrators can segment networks, enforce multi-factor authentication, and monitor activity continuously, ensuring that only authorized users interact with critical systems and data, significantly improving overall security posture.
Fortinet NSE8 Advanced Expertise
High-level network security expertise involves mastering advanced firewall, VPN, and threat mitigation strategies. The NSE8 811 exam validates a professional’s ability to design, deploy, and troubleshoot enterprise security solutions. Knowledge gained from this certification helps administrators implement sophisticated security policies in Check Point R81 environments, ensuring robust defenses.
Achieving advanced certification ensures professionals are prepared to handle large-scale, complex networks with multiple security layers. Their skills in configuring firewalls, monitoring threats, and integrating security solutions allow organizations to maintain high levels of protection against both internal and external attacks.
Fortinet NSE8 812 Certification
The follow-up to NSE8 811 focuses on practical application and troubleshooting of advanced security scenarios. Preparing for NSE8 812 equips administrators with the ability to optimize network performance while enforcing stringent security measures, complementing their Check Point R81 expertise.
Professionals can leverage this knowledge to quickly identify misconfigurations, mitigate vulnerabilities, and streamline security operations. The certification emphasizes real-world problem-solving skills, ensuring that security teams can respond efficiently to incidents and maintain continuous protection across the network.
Health and Safety Certifications Integration
Although network security is the primary focus, understanding regulations related to health, safety, and professional standards is essential for comprehensive compliance. Exams like MBLEx provide knowledge about ethics, standards, and operational best practices, which can inform policies around secure handling of sensitive information and operational safety.
Integrating health and safety awareness with IT security policies ensures that administrative, operational, and physical controls align. Professionals can develop holistic policies that protect both data and people, contributing to a culture of responsibility, accountability, and operational excellence.
Asset Protection and Management
Security administrators must implement structured frameworks to manage assets and sensitive information. The APM-001 exam emphasizes asset management, risk assessment, and policy enforcement, complementing network security tasks performed in Check Point R81 environments. Effective asset protection reduces exposure to unauthorized access and potential breaches.
Strong asset management supports compliance, operational continuity, and risk mitigation. By monitoring asset usage, defining ownership, and implementing access controls, administrators create an environment where both digital and physical resources are protected effectively, ensuring organizational resilience.
Business Process Management Security
Understanding and securing business processes is critical in preventing workflow-related vulnerabilities. Certifications like BPM-001 cover the integration of security measures into business workflows, policy enforcement, and risk management. Check Point R81 administrators can leverage this knowledge to align security strategies with operational processes, enhancing efficiency and compliance.
Business process security ensures that procedures are executed consistently and securely. By integrating workflow controls with network protections, administrators can prevent accidental or malicious deviations, protect sensitive information, and maintain smooth operational continuity, which is critical in high-security environments.
Certified Business Analysis Fundamentals
Business analysis is essential for bridging the gap between technical solutions and organizational objectives. Professionals need to understand how to assess processes, gather requirements, identify inefficiencies, and make data-driven recommendations. Strong analytical skills allow administrators to anticipate potential security gaps and optimize IT workflows. These abilities are particularly important for managing complex environments like Check Point R81, where aligning business goals with network security policies ensures both operational efficiency and protection.
Strong analytical skills form the backbone of effective IT security management. Understanding how to assess processes, identify gaps, and make informed decisions is essential for administrators. Preparing for the CBAF-001 exam provides foundational knowledge on business analysis principles that complement Check Point R81 administration, enabling professionals to align technical solutions with organizational objectives.
Business analysis ensures that security initiatives are tied to business outcomes. By understanding workflows, risk exposure, and performance metrics, administrators can implement solutions that address real organizational needs, improving both security effectiveness and operational efficiency.
Data Center Protection Essentials
Securing data centers goes beyond controlling physical access. It involves managing network traffic, monitoring system activity, implementing layered defenses, and ensuring redundancy. Professionals must understand firewalls, intrusion detection, and disaster recovery plans to protect critical assets. Administrators managing Check Point R81 systems benefit from these skills by ensuring comprehensive protection across all layers of the infrastructure, minimizing risks and maintaining uptime.
Securing data centers requires a combination of physical, network, and application-level controls. Professionals preparing for CDCP-001 certification learn methods for safeguarding critical assets, monitoring access, and implementing layered security approaches that reinforce Check Point firewall deployments. These principles help protect sensitive information and maintain operational continuity.
By integrating data center protection measures with firewall and endpoint management, administrators reduce the risk of breaches, enhance redundancy, and ensure that critical systems remain available even under adverse conditions, supporting the organization’s strategic resilience.
IT Management Fundamentals
Managing IT environments effectively requires not only technical expertise but also leadership and organizational skills. Professionals must coordinate teams, allocate resources, and maintain service levels while enforcing security policies. A structured approach to IT management ensures that operations run smoothly, risks are minimized, and security solutions like Check Point R81 are implemented efficiently across the enterprise.
Effective IT management involves overseeing both infrastructure and personnel to ensure consistent performance and security. Preparing for the CITM-001 exam equips professionals with strategies to align IT operations with organizational goals, including risk assessment, policy enforcement, and resource allocation, which are critical when managing Check Point R81 systems in enterprise environments.
Strong IT management ensures that security policies are applied consistently and that operational workflows are efficient. Administrators who combine technical expertise with management skills can prioritize initiatives, allocate resources effectively, and maintain high standards across all IT processes.
Lean Six Sigma Black Belt Integration
Process improvement is crucial in cybersecurity operations to maintain efficiency and reduce errors. Lean Six Sigma Black Belt training teaches advanced statistical analysis, workflow optimization, and project leadership, which are applicable in optimizing security operations centers and firewall management workflows. Applying these techniques ensures that network policies are efficient, repeatable, and auditable in high-pressure environments.
Process improvement methodologies like Lean Six Sigma are valuable for optimizing IT security operations. Professionals studying CLSSBB learn advanced process analysis and optimization techniques, which can be applied to firewall policy reviews, incident response workflows, and security operations center procedures in Check Point environments.
Applying Lean Six Sigma principles helps reduce errors, streamline workflows, and enhance the efficiency of security teams. By systematically analyzing processes, administrators can identify bottlenecks, eliminate redundancies, and ensure that operational procedures support both performance and compliance goals.
Lean Six Sigma Green Belt Concepts
Foundational knowledge in process improvement allows teams to implement incremental changes that improve both efficiency and security. Professionals with Green Belt skills understand the use of basic statistical tools, data analysis, and project planning to optimize operations. These skills can be directly applied to managing firewall rules, monitoring traffic patterns, and enhancing incident response processes.
For professionals seeking a foundational understanding of process improvement, the CLSSGB exam provides guidance on quality control, performance metrics, and project management. These skills support the administration of Check Point R81 systems by enabling teams to evaluate network operations and implement data-driven improvements efficiently.
Green Belt knowledge allows administrators to monitor key performance indicators, assess the effectiveness of security policies, and introduce enhancements that increase both operational efficiency and overall network protection, ensuring consistent performance over time.
Cybersecurity Practitioner Skills
Every IT professional must understand core cybersecurity principles to protect systems against evolving threats. Cybersecurity practitioners learn to identify vulnerabilities, assess risk, and implement mitigation strategies across network, application, and endpoint layers. These skills are fundamental when integrating security solutions like Check Point R81 into enterprise environments, ensuring that critical data remains protected.
Understanding core cybersecurity principles is essential for protecting networks, systems, and data. The CPST exam focuses on threat identification, risk assessment, and mitigation strategies, which are critical for professionals managing Check Point R81 firewalls. Mastering these concepts ensures that administrators can proactively address vulnerabilities and reduce organizational risk.
A strong grasp of cybersecurity fundamentals supports the implementation of robust firewall rules, endpoint protections, and network monitoring strategies. This proactive approach enhances the organization’s ability to prevent attacks, detect anomalies, and respond effectively to security incidents.
Scrum Master Fundamentals
Agile methodologies are widely adopted in IT operations to improve project delivery and team coordination. Scrum principles help teams plan work efficiently, prioritize tasks, and iterate improvements. Security projects benefit from these practices by allowing teams to deploy updates, patch vulnerabilities, and adjust configurations dynamically while maintaining continuous security coverage.
Agile methodologies improve team coordination and project delivery, including IT security initiatives. Preparing for CSM-001 equips professionals with skills in sprint planning, task prioritization, and iterative improvement, which are applicable to Check Point R81 project deployments and ongoing network security management.
Adopting Agile practices ensures that security updates, firewall configurations, and incident responses are delivered efficiently. Teams can adapt quickly to emerging threats, coordinate effectively across departments, and continuously improve processes to maintain high standards of protection.
Incident and Breach Response Readiness
Organizations must be prepared to respond to cyber incidents rapidly to minimize impact. Incident and breach response training equips professionals to detect threats, contain breaches, and restore operations while preserving evidence. These procedures are critical for maintaining compliance and protecting sensitive assets in environments secured by Check Point R81 systems.
Preparedness is critical when responding to cybersecurity incidents. The ICBRR exam focuses on strategies for detecting, analyzing, and mitigating breaches, which directly complement Check Point R81 incident response protocols. Skilled professionals can contain threats, preserve evidence, and restore normal operations efficiently.
Having robust incident response procedures minimizes downtime and potential damage from cyberattacks. Administrators trained in breach response are able to coordinate cross-functional teams, implement containment measures, and analyze events to prevent recurrence, improving the organization’s overall resilience.
Secure Coding and Review Practices
Security is more effective when integrated into the development lifecycle. Professionals who understand secure coding can identify vulnerabilities early, enforce coding standards, and perform thorough reviews. This proactive approach reduces the likelihood of exploits reaching production systems and complements network-level protections provided by Check Point R81 firewalls.
Developers and administrators alike benefit from understanding secure coding principles. Preparing for SCR exam teaches how to identify vulnerabilities, perform code reviews, and enforce best practices that reduce security risks. Integrating these practices with Check Point R81 firewall configurations ensures a comprehensive approach to organizational cybersecurity.
Secure coding knowledge prevents exploitation of software vulnerabilities that could bypass network defenses. By collaborating with development teams and enforcing standards, security professionals help create safer applications, reduce attack surfaces, and strengthen overall network protection strategies.
Cloud Infrastructure Certification
Cloud adoption has created the need for specialized security skills, including identity management, monitoring, and compliance. Professionals trained in cloud security can ensure that cloud resources are properly configured, access is controlled, and sensitive information is protected. Integrating these measures with firewall policies enhances hybrid network defenses.
Cloud environments require specialized security measures to protect sensitive data and manage access controls. Professionals pursuing CIC-101-01 gain expertise in cloud security architecture, monitoring, and compliance, which complements Check Point R81 firewall policies in hybrid IT environments, ensuring continuous protection.
Securing cloud infrastructure involves monitoring configurations, enforcing access policies, and auditing activity for potential threats. Administrators who understand cloud security principles can integrate firewall controls, encryption protocols, and identity management solutions to create a unified, secure environment across on-premises and cloud platforms.
Conclusion
Mastering cybersecurity requires a combination of technical expertise, strategic thinking, and process-oriented approaches. Modern organizations face increasingly complex threats, ranging from sophisticated network attacks to vulnerabilities in cloud environments and applications. Professionals in IT security must be prepared to anticipate, detect, and respond to these threats with precision and agility. This requires a deep understanding of network infrastructures, firewalls, endpoint protection, and advanced monitoring tools, coupled with the ability to align security strategies with business goals and compliance requirements.
Building a strong foundation in both network and application security is essential. Administrators must understand how traffic flows through complex networks, how firewalls and intrusion prevention systems enforce policies, and how cloud and hybrid environments can be secured without hindering performance. Knowledge of database management, secure coding practices, and threat analytics further strengthens the ability to detect anomalies and prevent unauthorized access. When these technical skills are combined with best practices in process optimization, teams can achieve consistent and measurable improvements in operational efficiency and security outcomes.
Process improvement and project management play an equally vital role in maintaining a secure environment. Methodologies like Lean Six Sigma and Agile frameworks allow security teams to evaluate workflows, remove inefficiencies, and adapt quickly to evolving challenges. By systematically analyzing processes and implementing iterative improvements, organizations can ensure that both preventive and reactive measures are effective, repeatable, and auditable. Clear communication, role accountability, and collaboration across teams help create a culture of security awareness that permeates every level of the organization.
Proactive threat management is another critical aspect of modern cybersecurity. Professionals must not only respond to incidents but also anticipate emerging risks through continuous monitoring, real-time analytics, and advanced detection techniques. Endpoint security, secure cloud practices, and SIEM (Security Information and Event Management) capabilities allow teams to maintain visibility across networks and systems, ensuring that potential vulnerabilities are mitigated before they are exploited. This holistic approach reduces downtime, protects sensitive data, and enhances organizational resilience.
Finally, the integration of technical mastery, strategic planning, and operational excellence defines the standard for successful IT security professionals. By cultivating skills across multiple disciplines—including network architecture, cloud security, data management, process improvement, and incident response—security administrators can implement robust, adaptive, and sustainable defenses. Organizations benefit from reduced risk exposure, improved compliance, and optimized workflows, while professionals strengthen their expertise and career potential in a rapidly evolving digital landscape. Continuous learning, practical experience, and certification-based validation ensure that security teams remain prepared for future challenges, supporting long-term stability, efficiency, and resilience.