Exam Code: 156-315.81
Exam Name: Check Point Certified Security Expert R81
Certification Provider: Checkpoint
Corresponding Certification: CCSE R81
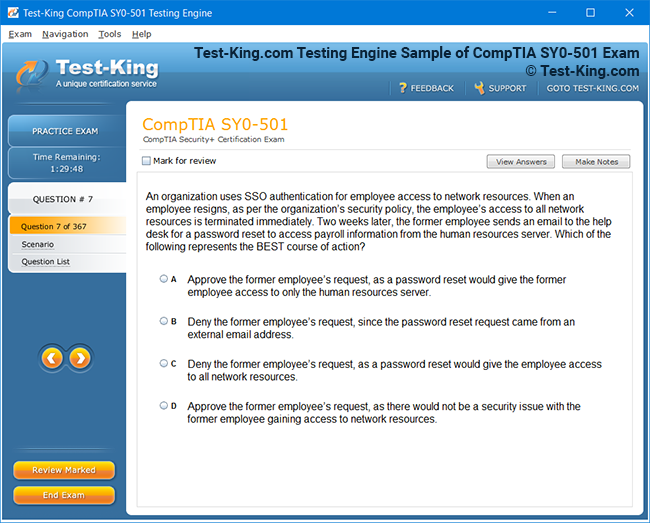
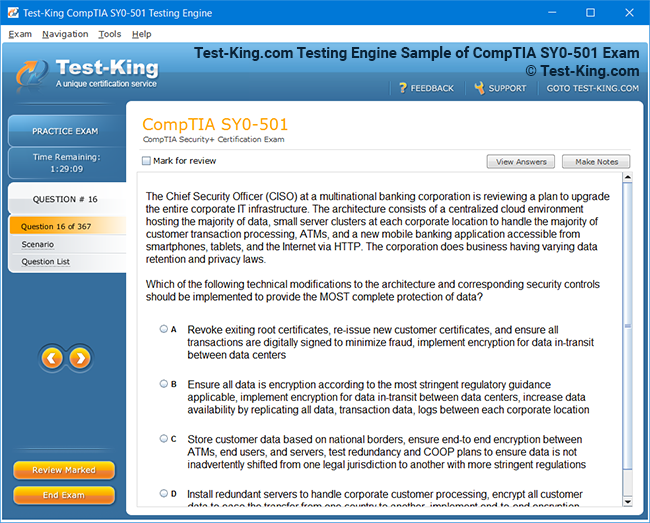
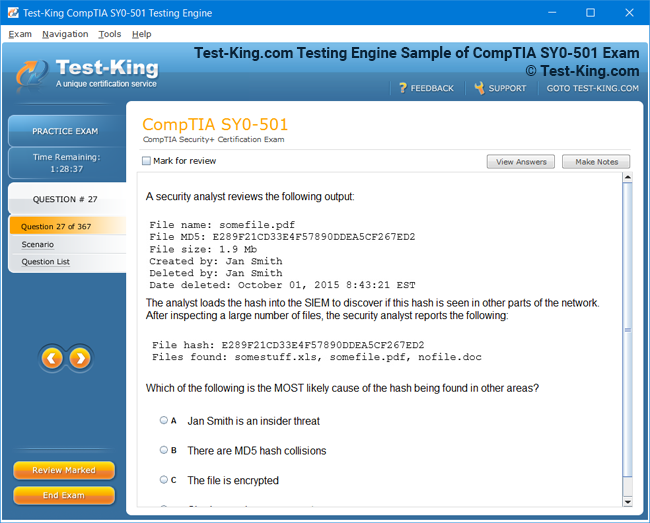
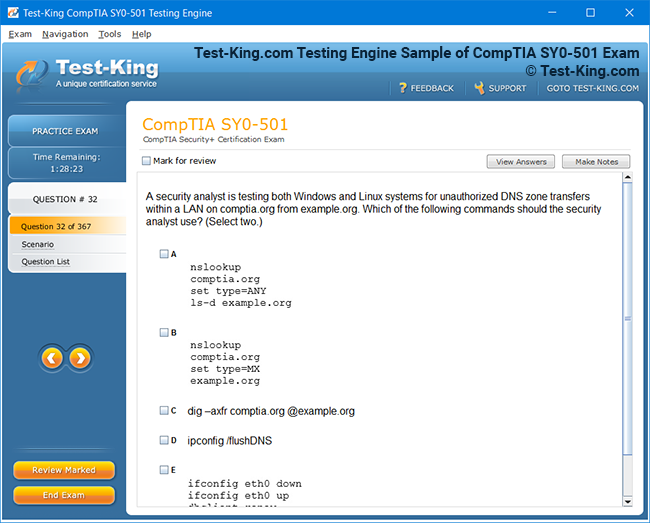
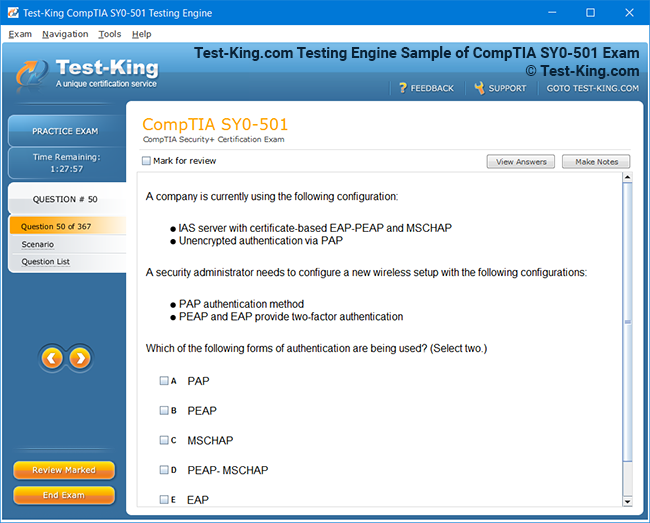
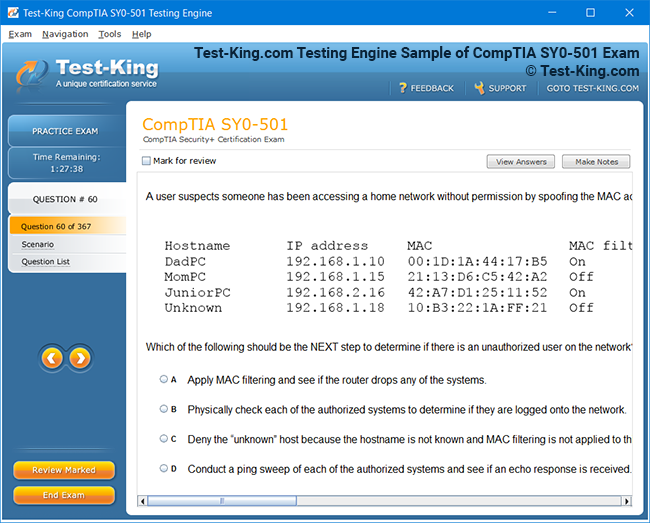
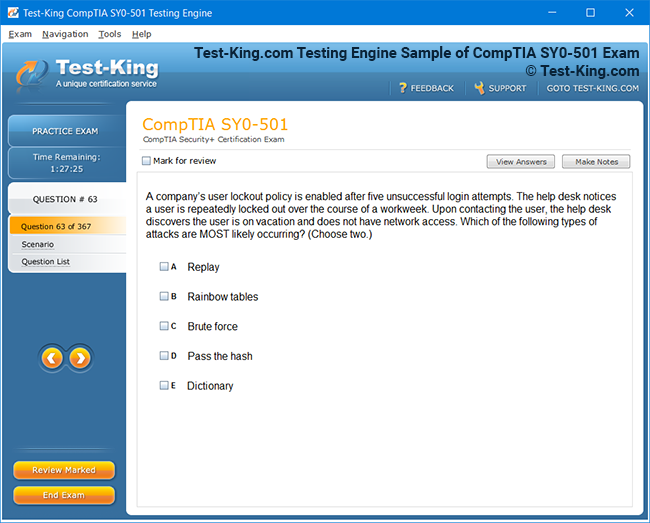
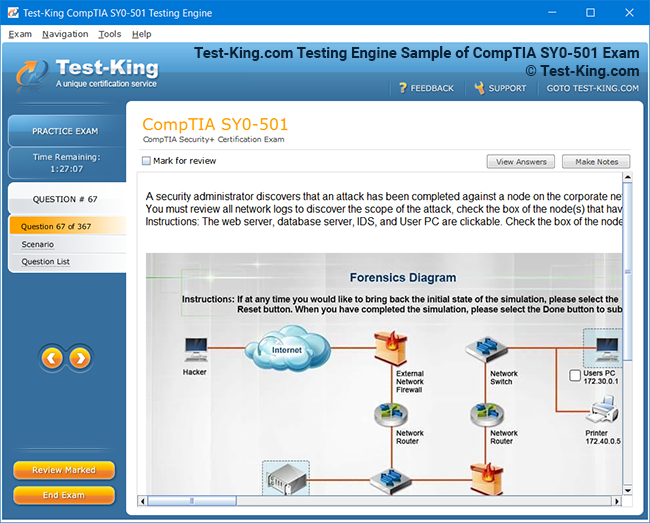
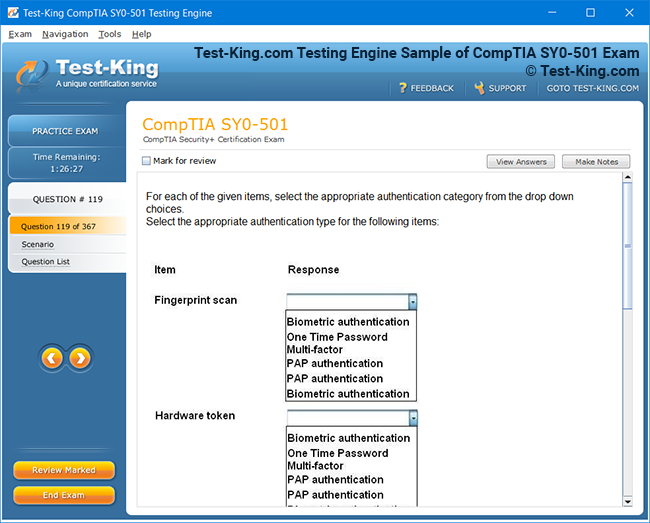
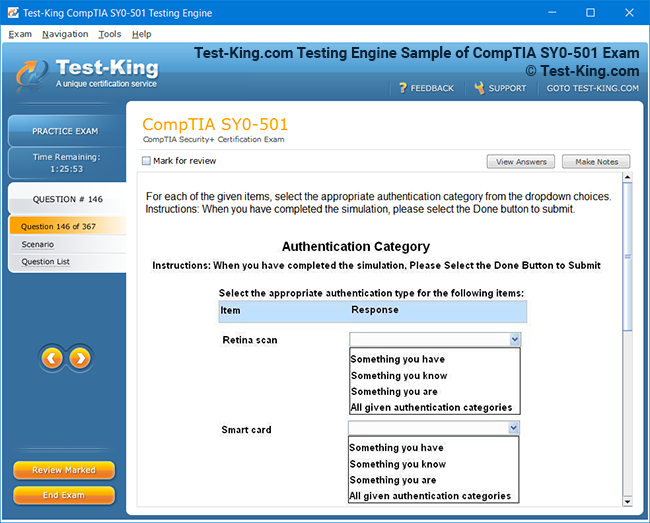
Product Screenshots
Frequently Asked Questions
How can I get the products after purchase?
All products are available for download immediately from your Member's Area. Once you have made the payment, you will be transferred to Member's Area where you can login and download the products you have purchased to your computer.
How long can I use my product? Will it be valid forever?
Test-King products have a validity of 90 days from the date of purchase. This means that any updates to the products, including but not limited to new questions, or updates and changes by our editing team, will be automatically downloaded on to computer to make sure that you get latest exam prep materials during those 90 days.
Can I renew my product if when it's expired?
Yes, when the 90 days of your product validity are over, you have the option of renewing your expired products with a 30% discount. This can be done in your Member's Area.
Please note that you will not be able to use the product after it has expired if you don't renew it.
How often are the questions updated?
We always try to provide the latest pool of questions, Updates in the questions depend on the changes in actual pool of questions by different vendors. As soon as we know about the change in the exam question pool we try our best to update the products as fast as possible.
How many computers I can download Test-King software on?
You can download the Test-King products on the maximum number of 2 (two) computers or devices. If you need to use the software on more than two machines, you can purchase this option separately. Please email support@test-king.com if you need to use more than 5 (five) computers.
What is a PDF Version?
PDF Version is a pdf document of Questions & Answers product. The document file has standart .pdf format, which can be easily read by any pdf reader application like Adobe Acrobat Reader, Foxit Reader, OpenOffice, Google Docs and many others.
Can I purchase PDF Version without the Testing Engine?
PDF Version cannot be purchased separately. It is only available as an add-on to main Question & Answer Testing Engine product.
What operating systems are supported by your Testing Engine software?
Our testing engine is supported by Windows. Andriod and IOS software is currently under development.
Top Checkpoint Exams
- 156-315.82 - Check Point Certified Security Expert - R82 (CCSE)
- 156-215.82 - Check Point Certified Security Administrator R82
- 156-587 - Check Point Certified Troubleshooting Expert - R81.20 (CCTE)
- 156-315.81.20 - Check Point Certified Security Expert - R81.20
- 156-215.81.20 - Check Point Certified Security Administrator - R81.20 (CCSA)
- 156-835 - Check Point Certified Maestro Expert
- 156-582 - Check Point Certified Troubleshooting Administrator - R81.20 (CCTA)
- 156-536 - Check Point Certified Harmony Endpoint Specialist - R81.20 (CCES)
- 156-560 - Check Point Certified Cloud Specialist (CCCS)
- 156-585 - Check Point Certified Troubleshooting Expert
156-315.81: Understanding the R81 Security Architecture for Exam Success
The 156-315.81 certification, formally known as the Check Point Certified Security Expert for R81, stands as one of the most respected and technically demanding credentials available to network security professionals working within the Check Point ecosystem. This certification validates a deep level of expertise in deploying, configuring, managing, and troubleshooting Check Point's security infrastructure at a level that goes far beyond what the entry-level administrator credential requires. Organizations that deploy Check Point solutions at enterprise scale actively seek professionals who hold this credential because it demonstrates the kind of advanced technical knowledge that translates directly into more secure, more reliable, and better-performing security environments.
What makes the CCSE particularly significant is its focus on the complete security management lifecycle rather than just surface-level configuration tasks. Candidates who earn this certification have demonstrated the ability to work with Check Point's SmartConsole management interface at an advanced level, implement complex security policies, configure clustering and high availability solutions, manage VPN architectures, perform advanced troubleshooting using command-line tools, and optimize gateway performance. These are skills that make a measurable difference in the quality and reliability of the security infrastructure that an organization depends on to protect its most sensitive data and critical systems.
R81 Architecture and Components
The R81 release represents one of the most significant updates to Check Point's security platform in recent years, introducing architectural improvements and new capabilities that affect how security administrators design, deploy, and manage their environments. At its core, the R81 architecture is built around three primary components that work together to deliver comprehensive network security: the Security Gateway, which enforces policy on network traffic; the Security Management Server, which stores policy and configuration data and distributes it to gateways; and SmartConsole, the administrative client through which security engineers interact with the entire environment. Understanding how these components interact is foundational to everything else covered in the CCSE exam.
The distributed architecture of Check Point's platform gives organizations the flexibility to deploy security components in configurations that match their specific operational requirements, from small single-site installations where the management server and gateway run on the same appliance to large enterprise environments with dozens of gateways managed from a centralized management server with full redundancy and high availability. R81 enhanced this architecture with improvements to the policy installation process, Unified Policy capabilities that allow multiple policy types to be managed from a single rule base, and performance improvements to the underlying security kernel that make gateway enforcement faster and more efficient at scale.
SmartConsole Management Interface
SmartConsole is the primary administrative interface through which Check Point security engineers configure policies, manage objects, monitor gateway status, and perform the full range of administrative tasks that the CCSE exam covers. R81 brought significant improvements to SmartConsole, including a modernized interface layout, improved policy search capabilities, and a new Infinity Portal integration that extends management capabilities to cloud-based security services. Candidates who want to perform well on the CCSE exam must develop genuine fluency with SmartConsole because a large portion of the exam's scenario-based questions involve identifying the correct SmartConsole workflow for a given administrative task.
Working effectively with SmartConsole requires more than knowing where menu items are located. It requires understanding the underlying logic of how Check Point organizes security objects, policies, and administrative permissions within the management database. Network objects, service objects, and security profiles must be created and organized in ways that make policy management efficient and maintainable as the environment grows. CCSE candidates must also understand how SmartConsole's multi-administrator environment works, including how policy locking, session management, and publish workflows prevent conflicts when multiple administrators are working in the same environment simultaneously.
Security Policy Construction Rules
Security policy construction is at the heart of the Check Point security engineer's daily work, and the CCSE certification tests candidates at a level of depth that requires not just knowing how to create rules but understanding the strategic principles that make a policy effective, maintainable, and performant. A Check Point security policy is a rule base composed of individual rules that define what traffic is allowed, what is blocked, what is logged, and what is subjected to additional inspection by security blades. The order in which rules appear in the rule base matters enormously because Check Point evaluates rules sequentially from top to bottom and applies the first matching rule it encounters.
Advanced policy construction at the CCSE level includes working with multiple policy layers, which R81 introduced as a way to organize complex rule bases into logical sections that can be managed independently and even shared across multiple gateways. Inline layers allow administrators to create sub-policies within specific rules, providing a way to handle complex traffic scenarios with fine-grained control without cluttering the main rule base. The CCSE exam tests candidates on how to design and implement layered policies correctly, including how to configure layer sharing, how traffic traverses multiple layers, and how logging and inspection settings interact across layered rule bases.
ClusterXL High Availability Configuration
High availability is a critical requirement for enterprise security infrastructure, and Check Point's ClusterXL technology provides the mechanism through which multiple Security Gateways can operate together to eliminate single points of failure and distribute traffic load. The CCSE certification places significant emphasis on ClusterXL because it is a technology that virtually every enterprise Check Point deployment uses, and configuring it correctly requires a detailed understanding of how the cluster members communicate, synchronize state, and handle failover events. A misconfigured cluster can result in traffic disruption during failover or, worse, incorrect enforcement of security policy during normal operation.
ClusterXL supports two primary deployment modes that serve different purposes and have different implications for how traffic is handled. High Availability mode keeps one cluster member active while others remain in standby, taking over only when the active member fails, which is the right choice for environments where simplicity and predictability of failover behavior are the primary concerns. Load Sharing mode distributes traffic across all active cluster members simultaneously, providing both redundancy and performance scaling, which suits environments with high traffic volumes that benefit from parallel processing across multiple gateway instances. CCSE candidates must understand the configuration steps, synchronization requirements, and failover behaviors of both modes to perform well on the exam.
VPN Architecture and Deployment
Virtual private network configuration is one of the most extensive topic areas in the CCSE certification, reflecting the central role that VPN technology plays in enterprise security architectures that need to provide secure connectivity for remote users, branch offices, and partner organizations. Check Point's VPN implementation supports both site-to-site VPN for connecting fixed locations and remote access VPN for individual users, with a rich set of configuration options that give security engineers precise control over encryption parameters, authentication methods, and traffic routing behavior through the VPN tunnel.
The CCSE exam tests candidates on the full VPN configuration workflow, from defining VPN communities that group the gateways participating in a VPN relationship to configuring encryption domain settings that determine which traffic is routed through the tunnel. Candidates must also understand how to configure VPN routing correctly in environments where traffic between VPN communities must be routed through a central hub gateway, a topology known as hub-and-spoke that is common in enterprise environments where centralized security inspection of all traffic is a requirement. Troubleshooting VPN connectivity issues using Check Point's command-line diagnostic tools is another area where the exam tests applied knowledge that candidates can only develop through hands-on practice.
Acceleration and Security Blades
Check Point's Software Blade architecture is a modular approach to security functionality that allows organizations to enable precisely the security capabilities they need on each gateway without paying for or running features they do not require. Each security blade adds a specific capability to the gateway, such as firewall, intrusion prevention, application control, URL filtering, antivirus, anti-bot, or data loss prevention. The CCSE exam requires candidates to understand how the major security blades work individually and how they interact when multiple blades are active on the same gateway, including how enabling certain combinations of blades affects performance and policy configuration.
SecureXL is Check Point's hardware and software acceleration technology that works alongside the security blade architecture to improve gateway throughput by offloading certain types of traffic processing from the main inspection path. When SecureXL identifies traffic that has already been inspected and can be safely forwarded based on established session state, it routes that traffic through an accelerated path that bypasses full inspection, dramatically increasing the number of connections per second the gateway can handle. CCSE candidates must understand how SecureXL works, how to verify its operation using command-line tools, and how certain security blade features interact with SecureXL acceleration in ways that affect which traffic qualifies for the accelerated path.
Multi-Domain Security Management
Multi-Domain Security Management is an enterprise-scale feature that allows a single Check Point management infrastructure to host multiple independent security domains, each with its own policy, object database, and administrative scope. This capability is particularly valuable for large organizations with distinct business units that require separate security management, for managed security service providers who manage security on behalf of multiple customers, and for organizations with geographically distributed operations that benefit from local management autonomy within a globally centralized infrastructure. The CCSE certification covers Multi-Domain Management because it is a technology that security engineers in enterprise and service provider environments regularly work with.
The architecture of a Multi-Domain environment adds layers of management hierarchy beyond what exists in a standard Check Point deployment. At the top level sits the Multi-Domain Server, which hosts the individual Domain Management Servers that each manage the security infrastructure of a specific domain. A Global Policy layer allows administrators at the top level to define policies that apply consistently across all domains, ensuring that organization-wide security requirements are enforced even when individual domains manage their own local policies. CCSE candidates must understand how to navigate this hierarchy, how to configure global policies, and how changes at the global level are pushed down to affect domain-level enforcement.
Threat Prevention Configuration Skills
Threat prevention is a broad category of security functionality that encompasses several Check Point security blades working together to detect and block malicious activity across multiple threat vectors. The IPS blade inspects traffic for known attack signatures and behavioral patterns associated with exploitation attempts, the Anti-Bot blade detects communications between infected hosts and command-and-control infrastructure, the Antivirus blade scans file transfers for known malware, and the Threat Emulation blade provides sandboxing capabilities that allow suspicious files to be executed in an isolated environment before they reach their destination. Configuring these blades effectively requires understanding both their individual settings and how they interact as a coordinated threat prevention system.
The CCSE exam tests candidates on how to configure threat prevention profiles that are tuned appropriately for different environments and traffic types. A profile that is appropriate for an internet-facing gateway handling untrusted external traffic may be unnecessarily aggressive for internal east-west traffic between trusted network segments, potentially causing performance overhead without proportional security benefit. CCSE candidates must understand how to use Check Point's predefined threat prevention profiles as starting points, how to customize them based on specific environmental requirements, and how to use the Threat Prevention policy to apply different profiles to different traffic flows based on source, destination, and service characteristics.
Identity Awareness and Access Control
Identity Awareness is a Check Point security blade that extends the traditional source IP-based access control model to include user identity as a policy criterion, enabling security engineers to write rules that apply to specific users or user groups regardless of which device or IP address they are connecting from. This capability is increasingly important in environments where users connect from multiple devices, work remotely from variable IP addresses, or share workstations in ways that make IP-based identification unreliable. The CCSE certification covers Identity Awareness configuration because it is a feature that significantly enhances the granularity and accuracy of security policy enforcement in modern enterprise environments.
Implementing Identity Awareness requires configuring identity acquisition methods that allow Check Point gateways to associate network connections with user identities in real time. The most common acquisition methods include Active Directory Query, which extracts login events from Windows domain controllers, the Identity Agent, which runs on individual user workstations and reports identity directly to the gateway, and Captive Portal, which prompts users to authenticate through a web browser when their identity cannot be determined by other means. CCSE candidates must understand how each acquisition method works, when each is most appropriate, and how to configure the integration between Check Point's identity infrastructure and Active Directory or other identity providers.
Logging Monitoring and SmartEvent
Comprehensive logging and monitoring are essential components of an effective security program, and Check Point's logging infrastructure provides the data foundation that security operations teams rely on for incident detection, investigation, and compliance reporting. The CCSE certification covers Check Point's logging architecture in detail, including how gateways generate log records, how those records are transmitted to the SmartLog server or Security Management Server for storage, and how administrators can search, filter, and analyze log data through SmartConsole's log viewing interface. Candidates must understand how to configure logging settings within the security policy to ensure that the right events are captured at the appropriate level of detail.
SmartEvent is Check Point's security event management and correlation capability that analyzes the stream of log data from Check Point gateways and applies correlation rules to identify patterns of activity that may indicate a security incident. Unlike raw log viewing, which presents individual events in isolation, SmartEvent groups related events together into a higher-level view that makes it easier for security analysts to recognize attack campaigns, identify compromised hosts, and prioritize their response efforts. CCSE candidates must understand how SmartEvent is configured, how correlation policies are managed, and how to use the SmartEvent interface to investigate security incidents effectively using the correlated event data it presents.
Advanced Troubleshooting Command Tools
Troubleshooting is one of the areas where the difference between a competent Check Point administrator and a true security expert is most clearly visible, and the CCSE certification tests candidates at a level that requires genuine command-line proficiency. The Gaia operating system that runs on Check Point appliances provides a rich set of diagnostic and debugging tools that experienced engineers use to investigate connectivity issues, verify policy enforcement, analyze traffic flows, and diagnose performance problems. Candidates who have spent time developing real command-line skills on Check Point gateways will find this section of the exam significantly more approachable than those who have relied exclusively on graphical interfaces.
Key troubleshooting tools that CCSE candidates must be proficient with include fw monitor, which provides packet-level visibility into traffic as it passes through different stages of firewall processing; cpd and fwd process management commands that allow administrators to check the status of and interact with core Check Point processes; the kernel debug facility that provides detailed insight into how the security kernel is handling specific traffic flows; and the cpinfo utility that collects comprehensive diagnostic data from a gateway for offline analysis or submission to Check Point technical support. Each of these tools serves specific diagnostic purposes, and knowing when and how to use each one is a mark of the advanced expertise that the CCSE certification is designed to validate.
Gaia Operating System Administration
The Gaia operating system is the unified platform on which Check Point Security Gateways and Security Management Servers run, combining elements of a hardened Linux distribution with Check Point-specific management interfaces and security features. CCSE candidates must be comfortable working with Gaia at both the graphical WebUI level and the command-line interface level, as both are used regularly in enterprise Check Point administration. The Gaia portal provides a web-based interface for network configuration, routing, system administration, and software management tasks, while the expert mode command line provides access to the full Linux shell for advanced diagnostic and configuration work.
Important Gaia administration topics covered in the CCSE curriculum include network interface configuration, static and dynamic routing setup using OSPF and BGP, system backup and restore procedures, software update management through CPUSE, and the configuration of management access controls that restrict who can connect to the Gaia administrative interfaces. Candidates must also understand how Gaia's role-based administration works, including how to create administrator accounts with appropriate privilege levels and how those privilege levels interact with the Check Point management permissions that are separately configured in SmartConsole. A solid grounding in Gaia administration provides the foundation for the advanced troubleshooting and configuration tasks that dominate the more challenging sections of the CCSE exam.
Exam Study and Lab Approach
Preparing for the 156-315.81 exam demands a study approach that prioritizes hands-on experience alongside conceptual learning, because the scenario-based questions that make up a significant portion of the exam require applied knowledge that cannot be developed through reading alone. Check Point's official training program includes an instructor-led CCSE course that provides structured coverage of all exam domains along with supervised lab exercises, and completing this training is strongly recommended as the foundation of any serious preparation effort. The labs included in official training introduce candidates to the configuration workflows and troubleshooting techniques that the exam tests, though additional independent practice is necessary to develop genuine fluency.
Setting up a personal Check Point lab environment using virtual machines is highly practical for CCSE preparation because Check Point provides evaluation licenses that allow candidates to run fully functional Security Management Server and Security Gateway instances in a virtualized environment. Working through realistic configuration scenarios in this environment, including deploying ClusterXL, configuring site-to-site VPN between multiple gateways, implementing threat prevention profiles, and troubleshooting deliberate misconfigurations using command-line tools, builds the kind of experiential knowledge that scenario questions test directly. Candidates who combine official training, independent lab practice, and systematic review of the exam objectives using Check Point's published blueprint will be well-positioned to approach the exam with confidence.
Post Certification Career Pathways
Earning the CCSE R81 certification creates meaningful professional opportunities for security engineers who want to advance their careers in the network security field. Organizations running Check Point infrastructure at enterprise scale need engineers who can go beyond routine administration to design, optimize, and troubleshoot complex security environments, and the CCSE is the credential that signals this level of capability most clearly within the Check Point ecosystem. Security engineers who hold the CCSE frequently take on roles as senior security engineers, security architects, or technical leads responsible for the overall health and performance of their organization's Check Point environment.
For professionals working at or aspiring to join managed security service providers, the CCSE is particularly valuable because these organizations manage Check Point environments on behalf of multiple customers and need engineers who can handle a wide range of complex scenarios independently without escalating to vendor support for routine advanced tasks. The certification also provides a strong foundation for pursuing the Check Point Certified Master credential, which represents the pinnacle of technical expertise in the Check Point certification hierarchy and opens doors to the most senior and specialized security engineering roles available. In either case, the CCSE represents a career investment that pays returns in the form of greater professional credibility, broader opportunity, and the satisfaction of working at the leading edge of enterprise network security practice.
Conclusion
The 156-315.81 Check Point Certified Security Expert certification for R81 is a rigorous and genuinely valuable credential for security professionals who work with or aspire to work with Check Point's enterprise security platform at an advanced technical level. The breadth and depth of knowledge it validates, spanning security policy architecture, high availability clustering, VPN design, threat prevention, identity-aware access control, advanced troubleshooting, and enterprise management capabilities, reflects the true complexity of the role that senior Check Point engineers play in protecting organizational infrastructure. Earning this certification requires a serious and sustained commitment to both conceptual learning and hands-on technical development that cannot be shortcut or approximated.
What the preparation process produces, beyond the credential itself, is a security engineer who understands Check Point's R81 platform at a level that makes them genuinely more effective in every aspect of their work. The engineer who has prepared thoroughly for the CCSE does not just know where to click in SmartConsole; they understand why policies are structured the way they are, how the underlying security kernel processes traffic, what happens at each stage of the inspection path when a packet traverses a gateway, and how to read diagnostic output to identify the precise point where a connectivity or enforcement issue originates. This depth of understanding is what distinguishes a security expert from a security administrator, and it is the quality that the CCSE certification is specifically designed to recognize and reward.
For organizations making hiring decisions about the professionals who will manage their Check Point security infrastructure, the CCSE provides a reliable and meaningful signal of technical capability that is difficult to assess through interviews alone. For the professionals themselves, it represents a milestone that reflects genuine achievement and opens doors to the kinds of senior, high-impact roles where their expertise can make a real difference to organizational security outcomes. In a security landscape that grows more complex and more consequential with each passing year, having professionals whose skills have been rigorously validated through a demanding certification process is not merely a nice credential to display but a practical operational advantage that shows up in the quality, reliability, and effectiveness of the security infrastructure they build and maintain every day for the organizations that trust them with their most critical protection responsibilities.