Exam Code: 300-720
Exam Name: Securing Email with Cisco Email Security Appliance (300-720 SESA)
Certification Provider: Cisco
Corresponding Certification: CCNP Security
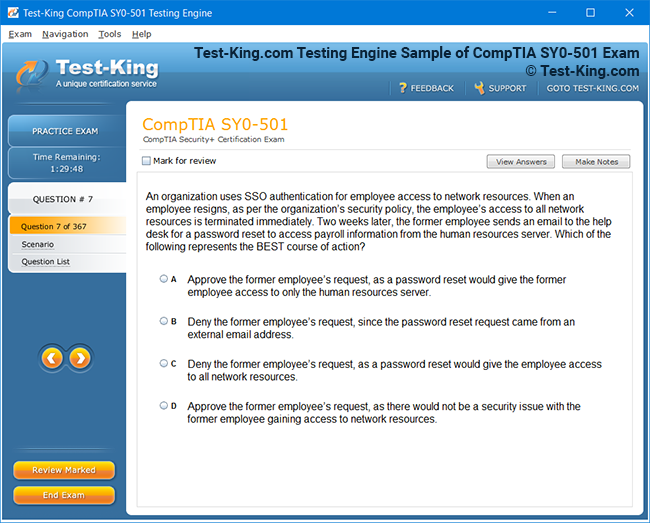
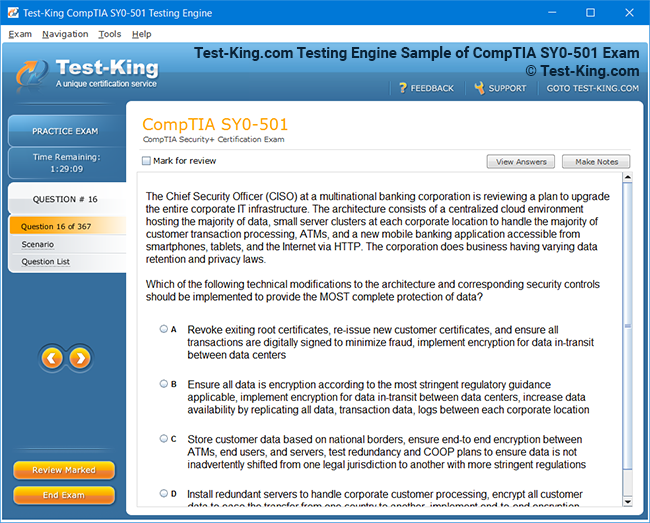
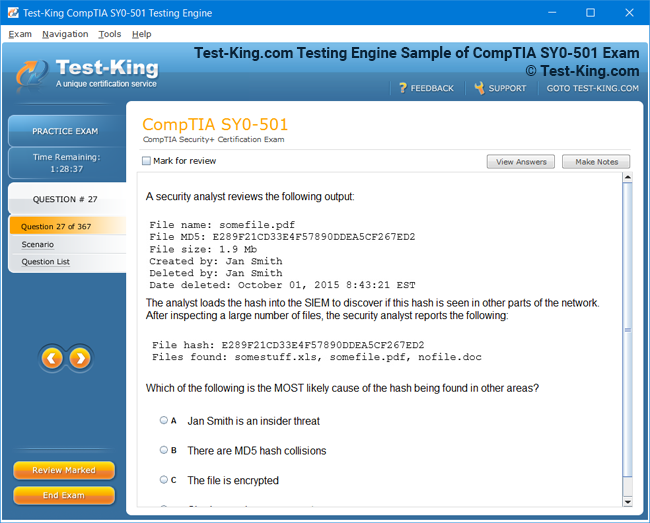
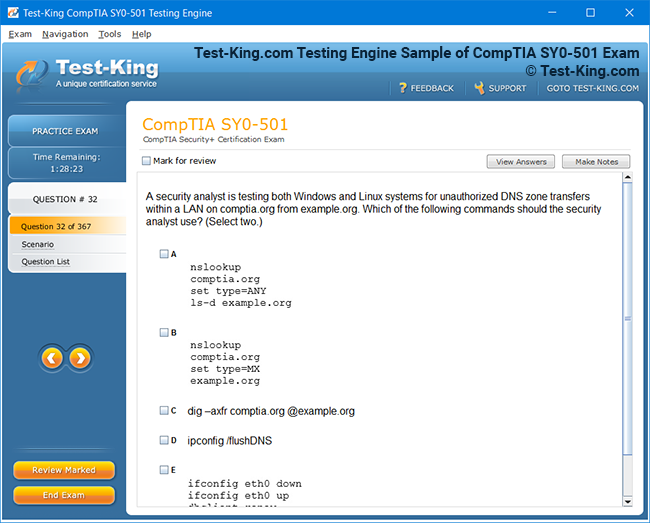
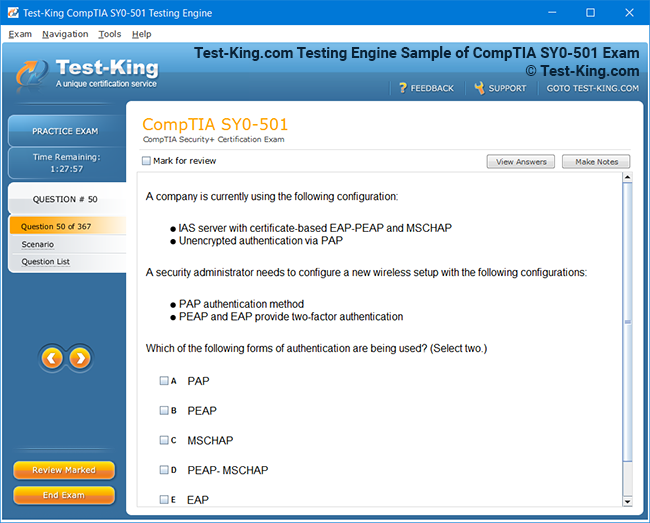
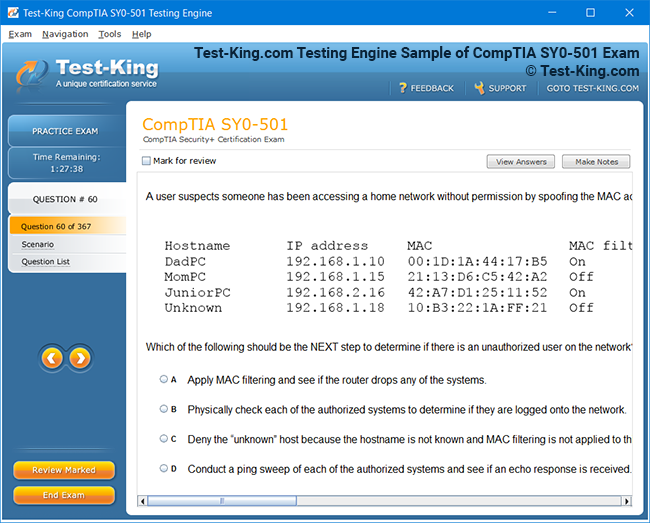
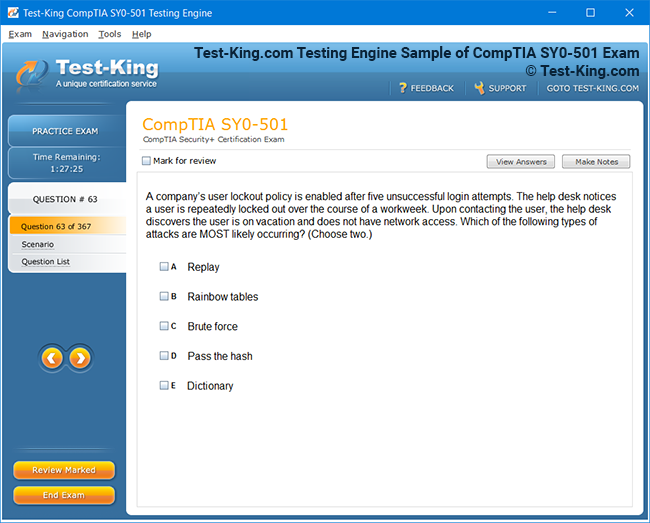
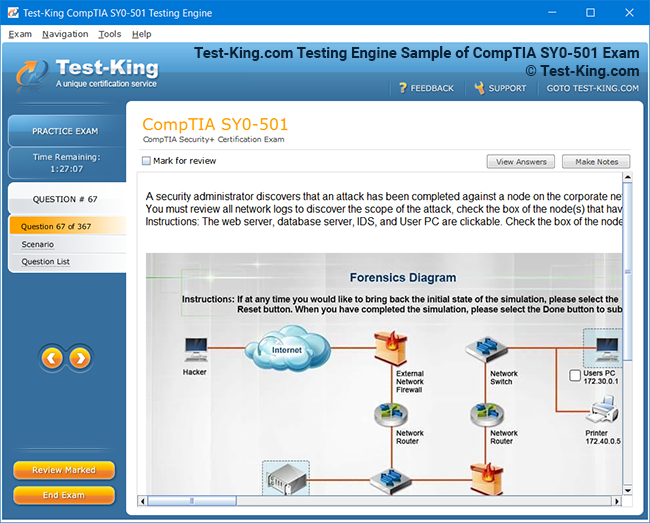
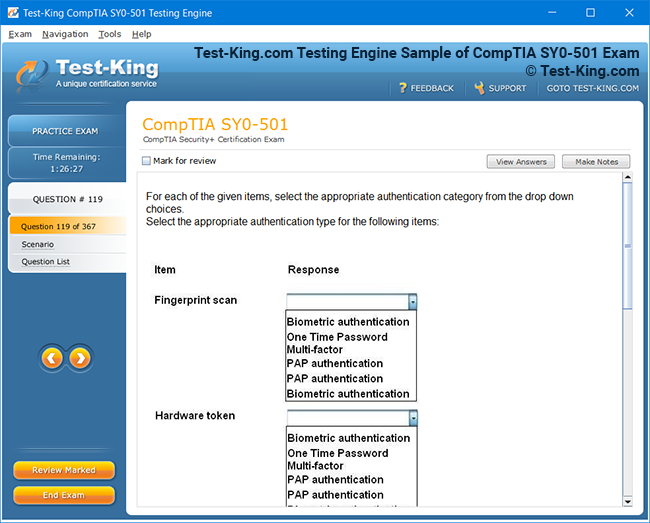
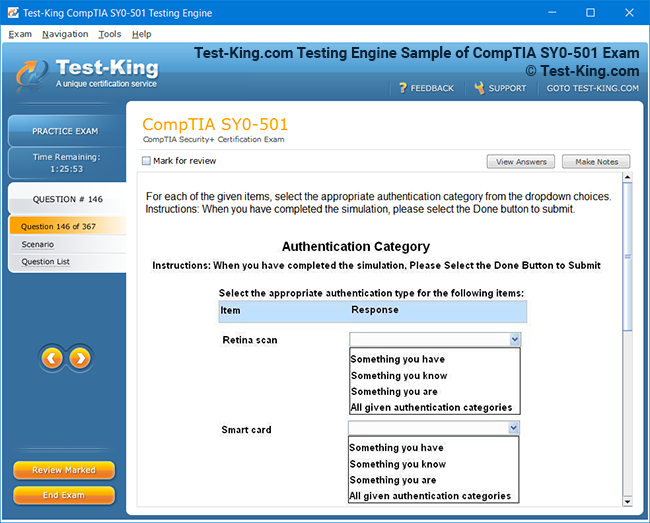
Product Screenshots
Frequently Asked Questions
How can I get the products after purchase?
All products are available for download immediately from your Member's Area. Once you have made the payment, you will be transferred to Member's Area where you can login and download the products you have purchased to your computer.
How long can I use my product? Will it be valid forever?
Test-King products have a validity of 90 days from the date of purchase. This means that any updates to the products, including but not limited to new questions, or updates and changes by our editing team, will be automatically downloaded on to computer to make sure that you get latest exam prep materials during those 90 days.
Can I renew my product if when it's expired?
Yes, when the 90 days of your product validity are over, you have the option of renewing your expired products with a 30% discount. This can be done in your Member's Area.
Please note that you will not be able to use the product after it has expired if you don't renew it.
How often are the questions updated?
We always try to provide the latest pool of questions, Updates in the questions depend on the changes in actual pool of questions by different vendors. As soon as we know about the change in the exam question pool we try our best to update the products as fast as possible.
How many computers I can download Test-King software on?
You can download the Test-King products on the maximum number of 2 (two) computers or devices. If you need to use the software on more than two machines, you can purchase this option separately. Please email support@test-king.com if you need to use more than 5 (five) computers.
What is a PDF Version?
PDF Version is a pdf document of Questions & Answers product. The document file has standart .pdf format, which can be easily read by any pdf reader application like Adobe Acrobat Reader, Foxit Reader, OpenOffice, Google Docs and many others.
Can I purchase PDF Version without the Testing Engine?
PDF Version cannot be purchased separately. It is only available as an add-on to main Question & Answer Testing Engine product.
What operating systems are supported by your Testing Engine software?
Our testing engine is supported by Windows. Andriod and IOS software is currently under development.
Top Cisco Exams
- 200-301 - Cisco Certified Network Associate (CCNA)
- 350-401 - Implementing Cisco Enterprise Network Core Technologies (ENCOR)
- 350-701 - Implementing and Operating Cisco Security Core Technologies
- 300-410 - Implementing Cisco Enterprise Advanced Routing and Services (ENARSI)
- 350-601 - Implementing and Operating Cisco Data Center Core Technologies (DCCOR)
- 300-715 - Implementing and Configuring Cisco Identity Services Engine (300-715 SISE)
- 300-710 - Securing Networks with Cisco Firewalls
- 400-007 - Cisco Certified Design Expert
- 200-901 - DevNet Associate (DEVASC)
- 350-501 - Implementing and Operating Cisco Service Provider Network Core Technologies (SPCOR)
- 350-801 - Implementing Cisco Collaboration Core Technologies (CLCOR)
- 300-420 - Designing Cisco Enterprise Networks (ENSLD)
- 300-415 - Implementing Cisco SD-WAN Solutions (ENSDWI)
- 200-201 - Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
- 300-620 - Implementing Cisco Application Centric Infrastructure (DCACI)
- 500-220 - Cisco Meraki Solutions Specialist
- 300-425 - Designing Cisco Enterprise Wireless Networks (300-425 ENWLSD)
- 100-150 - Cisco Certified Support Technician (CCST) Networking
- 300-730 - Implementing Secure Solutions with Virtual Private Networks (SVPN 300-730)
- 350-201 - Performing Cybersecurity Using Cisco Security Technologies (CBRCOR)
- 820-605 - Cisco Customer Success Manager (CSM)
- 300-510 - Implementing Cisco Service Provider Advanced Routing Solutions (SPRI)
- 300-815 - Implementing Cisco Advanced Call Control and Mobility Services (CLASSM)
- 300-430 - Implementing Cisco Enterprise Wireless Networks (300-430 ENWLSI)
- 300-435 - Automating Cisco Enterprise Solutions (ENAUTO)
- 300-515 - Implementing Cisco Service Provider VPN Services (SPVI)
- 300-440 - Designing and Implementing Cloud Connectivity (ENCC)
- 700-805 - Cisco Renewals Manager (CRM)
- 300-445 - Designing and Implementing Enterprise Network Assurance
- 300-720 - Securing Email with Cisco Email Security Appliance (300-720 SESA)
- 350-901 - Developing Applications using Cisco Core Platforms and APIs (DEVCOR)
- 300-725 - Securing the Web with Cisco Web Security Appliance (300-725 SWSA)
- 300-610 - Designing Cisco Data Center Infrastructure for Traditional and AI Workloads
- 300-635 - Automating Cisco Data Center Solutions (DCAUTO)
- 300-630 - Implementing Cisco Application Centric Infrastructure - Advanced
- 300-615 - Troubleshooting Cisco Data Center Infrastructure (DCIT)
- 500-445 - Implementing Cisco Contact Center Enterprise Chat and Email (CCECE)
- 100-140 - Cisco Certified Support Technician (CCST) IT Support
- 300-220 - Conducting Threat Hunting and Defending using Cisco Technologies for Cybersecurity
- 300-215 - Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR)
- 500-420 - Cisco AppDynamics Associate Performance Analyst
- 300-745 - Designing Cisco Security Infrastructure
- 100-160 - Cisco Certified Support Technician (CCST) Cybersecurity
- 500-470 - Cisco Enterprise Networks SDA, SDWAN and ISE Exam for System Engineers (ENSDENG)
- 300-820 - Implementing Cisco Collaboration Cloud and Edge Solutions
Understanding the Cisco 300-720 SESA Exam and Its Significance for Security Professionals
In today’s cybersecurity landscape, organizations face unprecedented challenges in safeguarding their communication channels, particularly email, which remains one of the most exploited attack vectors. Email serves as a central hub for internal collaboration, client communication, and the exchange of sensitive documents, making it a prime target for cybercriminals. Security breaches via email can have devastating consequences, including financial loss, data theft, and reputational damage. For professionals aiming to enhance their cybersecurity expertise, the ABT certification guide for IT professionals offers structured guidance on email security, highlighting industry standards and the practical skills required to defend enterprise communication systems. Through this framework, candidates gain insight into operational risks, threat vectors, and mitigation strategies, equipping them to safeguard organizations against evolving email-based attacks.
Email security is not just about preventing malicious messages from entering inboxes; it also encompasses protecting sensitive data from unauthorized exposure, ensuring compliance with regulatory standards, and maintaining business continuity. By adopting the structured approaches outlined in certification programs like ABT, professionals can evaluate existing defenses, implement multi-layered security strategies, and respond proactively to emerging threats. This foundational understanding is critical for those pursuing advanced certifications such as Cisco 300‑720 SESA, which focuses on operational deployment and management of email security appliances in enterprise environments.
Understanding Organizational Risk and Email Threats
Organizations rely heavily on email as their primary communication medium, making it a critical point of vulnerability. Threats such as phishing, spear-phishing, malware-laden attachments, business email compromise (BEC), and malicious links are increasingly sophisticated and capable of bypassing traditional defenses. Breaches through email can disrupt operations, damage client trust, and result in costly legal and regulatory consequences. Candidates preparing for advanced security roles can benefit from the 7497X exam preparation, which provides hands-on scenarios illustrating how email vulnerabilities are exploited and how proper configuration of security appliances mitigates risk.
The 7497X materials emphasize practical exercises that mirror real-world conditions, including identifying suspicious email characteristics, testing policy configurations, and analyzing system logs for potential threats. Understanding these risks equips professionals with the analytical skills needed to prioritize threat mitigation, evaluate security controls, and implement defense strategies that balance operational efficiency with protection. Moreover, structured preparation helps candidates anticipate attack vectors before they manifest in live environments, ensuring a proactive rather than reactive security posture.
The Cisco 300‑720 SESA Exam Overview
The Cisco 300‑720 Securing Email with Cisco Email Security Appliance (SESA) exam is designed to validate a professional’s ability to deploy, configure, and manage email security solutions using Cisco ESA. Unlike entry-level certifications that focus primarily on theoretical knowledge, the SESA exam emphasizes practical application, requiring candidates to demonstrate skills in policy management, threat defense deployment, traffic monitoring, and incident troubleshooting. The 7498X exam breakdown guide provides a comprehensive roadmap, offering detailed scenarios that replicate challenges faced by email security professionals in enterprise environments.
The exam ensures candidates understand not only the technical mechanisms of Cisco ESA but also the operational considerations of email security. For example, configuring policies too restrictively can prevent legitimate emails from reaching recipients, while lenient policies may leave organizations exposed to sophisticated attacks. SESA examines candidates’ ability to calibrate these policies effectively, balancing security needs with workflow continuity. Achieving this certification demonstrates a professional’s capacity for nuanced decision-making, critical thinking, and operational management under real-world conditions.
Foundational Security Concepts for Email Protection
Before mastering Cisco ESA configurations, candidates must develop a strong foundation in email security concepts. This includes understanding the behavior of email protocols like SMTP, differentiating between inbound and outbound threat vectors, and recognizing common attack patterns targeting corporate messaging systems. Supplemental materials, including the Pega PCSA credential overview, illustrate policy deployment strategies in structured environments, helping professionals contextualize abstract concepts and apply them effectively within Cisco ESA platforms.
Candidates are also encouraged to analyze historical case studies of email breaches, exploring how attackers exploit vulnerabilities to deliver malware, execute phishing campaigns, or compromise credentials. These studies reinforce critical thinking and problem-solving skills, allowing candidates to simulate risk assessment, evaluate mitigation strategies, and implement policy adjustments in controlled environments. A strong conceptual foundation ensures that professionals are equipped to respond to evolving threats systematically and effectively in operational scenarios.
The Critical Role of Policies in Email Security
Connection and content policies are central to email defense. Connection policies evaluate sender behavior, IP reputation, and domain legitimacy to determine whether messages should be accepted, rejected, or quarantined for further inspection. Content policies examine message headers, attachments, and embedded URLs for suspicious activity, ensuring malicious payloads are intercepted before reaching end users. Professionals can deepen their understanding of policy frameworks through the PeopleCert certification pathway, which emphasizes structured approaches to risk mitigation and rule-based control implementation.
Dynamic policy management is essential as attackers constantly modify tactics to evade detection. Candidates are trained to implement layered rulesets that adapt to emerging threats, balancing operational efficiency with security enforcement. For example, content policies may be configured to scan for encrypted attachments, suspicious macros, or known malware signatures while minimizing false positives. Integration of frameworks like PeopleCert strengthens systematic evaluation, continuous monitoring, and iterative improvement skills, which are directly applicable to both exam success and real-world operations.
Advanced Threat Defense Features
Modern email threats often bypass basic filtering mechanisms, necessitating the deployment of advanced defenses. Cisco ESA integrates features like sandboxing, URL filtering, and Advanced Malware Protection (AMP) to detect zero-day exploits, analyze suspicious files, and block malicious links. Exam candidates must understand how to configure these mechanisms effectively and respond to evolving attack scenarios. Analytical reasoning and structured problem-solving are reinforced through methodologies highlighted in CAPM credential guidelines, enabling candidates to approach advanced threat mitigation methodically.
Proficiency in advanced threat defense requires understanding the full attack lifecycle—from reconnaissance and delivery to exploitation and post-exploitation. Candidates practice simulating scenarios where malicious attachments attempt to bypass sandbox analysis or URLs attempt to evade URL filtering. Structured analytical approaches provide a framework for assessing risks, testing defensive measures, and implementing mitigation strategies that minimize organizational exposure while maintaining operational flow.
Monitoring Email Flow and System Health
Continuous monitoring and reporting are critical to maintaining robust email security. Professionals must interpret message logs, identify anomalies, and produce actionable insights to guide policy adjustments and incident response. The PfMP certification standards provide guidance on program-level analytics and data interpretation, which can be applied directly to email security monitoring and reporting.
Monitoring allows teams to detect recurring threat patterns, optimize filtering rules, and ensure compliance with internal and external security standards. By analyzing traffic trends and incident data, security professionals can anticipate emerging threats and implement proactive measures. Integrating structured analytical approaches from PfMP strengthens the connection between technical monitoring, operational decision-making, and strategic risk management, ensuring that email defenses remain robust and adaptive.
Ensuring Policy Compliance and Optimization
Maintaining effective policies requires understanding potential conflicts, overlaps, and unintended consequences. Overly restrictive rules can impede legitimate communication, whereas insufficiently rigorous policies may leave gaps exploitable by attackers. Professionals can refine their policy management skills using structured evaluation frameworks from PgMP certification insights, which emphasize systematic assessment, continuous optimization, and strategic alignment.
Candidates are trained to balance security enforcement with operational demands, testing configurations to ensure legitimate emails flow smoothly while malicious activity is blocked. Through iterative refinement, professionals learn to optimize policy sets, prioritize risk mitigation, and ensure consistent enforcement across enterprise systems. These skills are essential both for exam readiness and for operational roles where high-volume email traffic demands precision and reliability.
Adapting to Agile and Dynamic Threats
Email security is not static. Threat actors continually refine their tactics, making agility and adaptability essential for security professionals. Candidates preparing for the SESA exam benefit from methodologies used in PMI-ACP credential frameworks, which emphasize iterative approaches, rapid response, and adaptive planning. Applying these principles allows security teams to adjust rules, deploy countermeasures, and evaluate effectiveness in near real-time.
Agile approaches in email security involve regular review of threat intelligence, policy updates, and simulation of attack scenarios. Professionals learn to respond to zero-day vulnerabilities, newly discovered malware variants, and advanced phishing techniques by leveraging structured frameworks that promote iterative improvement. This ensures email systems remain resilient, and operational continuity is maintained despite evolving threats.
Managing Risk in Enterprise Email Systems
Enterprise email systems are critical assets, and their compromise can lead to cascading organizational impacts. Professionals must evaluate risk exposure, prioritize mitigation strategies, and implement effective controls to safeguard sensitive communication. By incorporating insights from PMI-RMP certification standards, candidates develop systematic approaches to risk identification, assessment, and mitigation, directly applicable to managing email security in large-scale environments.
Understanding risk management involves not only identifying technical vulnerabilities but also assessing human factors, regulatory compliance, and business process implications. Candidates are trained to anticipate attack vectors, respond to incidents, and continually evaluate policy effectiveness. This holistic approach ensures that email systems remain secure, threats are minimized, and the organization can operate confidently in complex digital environments.
The Importance of Automation in Email Security
Automation plays a crucial role in managing large-scale email systems. Manually applying policies to thousands of accounts is inefficient and error-prone, which increases exposure to threats. The Cisco ESA platform allows security teams to automate routine tasks like spam filtering, malware scanning, and URL inspection. To understand automation best practices more comprehensively, candidates often reference certification guidance like the 77-728 exam overview, which illustrates workflow optimization and automation principles applicable to large enterprise systems. By comparing automation strategies across different platforms, professionals can develop scalable, efficient, and secure operational routines that reduce human error.
Expanding on automation, candidates also learn to integrate real-time threat intelligence feeds, which allow the ESA to dynamically block suspicious messages without manual intervention. Automation also provides detailed audit trails, which simplify compliance reporting and incident investigations. Incorporating structured learning from certifications like 77-728 ensures professionals can design, deploy, and maintain automated email defenses that scale with organizational needs while maintaining high security standards.
Threat Intelligence and Real-Time Monitoring
A sophisticated email security strategy relies on actionable threat intelligence. The ESA can analyze patterns, detect anomalies, and correlate suspicious activity across multiple accounts. Candidates preparing for the SESA exam benefit from understanding concepts highlighted in other technical certification pathways, such as the 77-881 exam preparation guide, which provides insight into monitoring techniques and threat identification workflows. Understanding how to interpret telemetry data enables security engineers to proactively detect phishing campaigns or malware distribution before they impact the organization.
Real-time monitoring also allows teams to quickly adapt to new threat vectors, such as zero-day vulnerabilities or targeted attacks on executives. By leveraging threat intelligence effectively, candidates can create dynamic policies that adjust automatically to emerging risks. The combination of structured learning and hands-on simulation prepares security professionals to maintain continuous vigilance while ensuring email systems remain operational and secure.
Configuring Advanced Malware Protection
Advanced Malware Protection (AMP) is a cornerstone feature of Cisco ESA, designed to detect and mitigate sophisticated malware attempts. Understanding AMP’s configuration, including sandboxing and behavioral analysis, is critical for exam success. Professionals often find guidance in exams like 77-882 certification guide, which illustrates practical techniques for malware detection, analysis, and remediation. By learning to apply multi-layered defenses effectively, candidates gain the skills necessary to prevent malicious attachments, embedded scripts, and other forms of email-based malware from compromising organizational systems.
Proper configuration also involves evaluating historical threat data and establishing policies that minimize false positives. For instance, advanced rule tuning can differentiate between benign large attachments and potentially harmful files. By studying AMP through structured exercises, professionals ensure their systems remain proactive, adaptive, and resilient against evolving malware threats, a key competency validated in the SESA exam.
Policy Design and Enforcement
Designing effective policies is central to controlling email traffic and securing organizational communication. Connection and content policies determine how messages are processed, filtered, or blocked. Professionals often extend their understanding by examining frameworks like the 77-884 exam analysis, which emphasizes designing rules that align operational efficiency with risk management objectives. Properly designed policies balance security needs with user productivity, ensuring that legitimate communication is not unnecessarily disrupted while preventing exposure to phishing, spam, or malware attacks.
Candidates also learn to implement layered policies, combining sender verification, content scanning, and URL analysis to create a comprehensive defense strategy. Simulating real-world scenarios ensures that policies function as intended under varying load conditions and threat patterns. The combination of structured policy design and scenario-based testing is critical for both exam readiness and operational competence.
Compliance and Regulatory Integration
Email communications frequently carry sensitive information subject to regulatory oversight. Professionals must configure retention policies, data loss prevention (DLP) rules, and compliance reporting within the Cisco ESA. Understanding compliance integration is enhanced by examining exam frameworks such as 77-886 certification roadmap, which illustrates how technical configurations align with regulatory requirements. Knowledge of compliance requirements allows security engineers to implement email security measures that satisfy legal obligations while minimizing operational disruption.
Furthermore, integration of compliance into daily operations requires ongoing monitoring and reporting. Professionals must be able to generate audit-ready logs, track policy adherence, and respond to regulatory inquiries. Structured training ensures that candidates understand the nuances of compliance-driven security design and can confidently apply these principles within complex enterprise environments.
Reporting and Message Analytics
Generating actionable insights from message flow is another key skill for SESA candidates. The ESA provides detailed logs and reports that allow teams to track email delivery, detect anomalies, and assess policy effectiveness. For deeper insights, candidates can study parallels in other technical certifications like the 77-888 exam preparation, which covers data interpretation, reporting strategies, and performance analysis. Strong reporting skills enable professionals to identify systemic vulnerabilities, fine-tune policies, and present metrics that demonstrate the effectiveness of security interventions to management.
Analytics also supports incident response and risk assessment processes. By correlating log data across multiple vectors, security teams can uncover coordinated attacks, detect suspicious behavior patterns, and implement corrective measures proactively. Mastery of reporting tools is therefore essential not only for exam success but also for operational excellence in managing enterprise email systems.
Threat Mitigation Using Encryption
Encryption is a critical mechanism for securing email communication against interception, tampering, or unauthorized access. Candidates must understand how to implement secure transport protocols, such as TLS, and configure encryption policies within the ESA. Practical exercises, guided by frameworks like the 98-349 exam learning guide, reinforce the importance of protecting sensitive data during transmission. By understanding encryption workflows and their impact on system performance, candidates can design secure, compliant email environments that prevent data breaches and meet organizational standards.
Integrating encryption with content policies and threat detection mechanisms ensures multi-layered protection. Security professionals learn to maintain a balance between performance and security, applying selective encryption where sensitive information is involved while allowing standard processing for non-sensitive messages. This skill set is essential for securing enterprise communication channels effectively.
System Troubleshooting and Diagnostics
Effective troubleshooting is critical for maintaining continuous email service while enforcing strict security policies. The ESA provides diagnostic tools to analyze delivery issues, identify policy conflicts, and resolve system errors. Candidates can expand their troubleshooting proficiency by reviewing methodologies in other certification guides, such as the 98-361 exam preparation materials, which emphasize structured diagnostic techniques, problem resolution workflows, and system performance evaluation. Strong troubleshooting skills allow candidates to respond quickly to disruptions while minimizing impact on operations.
Hands-on lab exercises simulate real-world issues, including blocked messages, false positives, and misrouted emails. By systematically diagnosing root causes and applying corrective measures, professionals develop both the technical confidence and operational insight required to maintain secure and reliable email infrastructure under varying conditions.
Integrating ESA with Broader IT Systems
Cisco ESA functions optimally when integrated with other security solutions, such as endpoint protection, network monitoring, and Security Information and Event Management (SIEM) platforms. Exam candidates benefit from learning how to coordinate email security measures with broader IT ecosystem strategies, reinforced through certifications like the 98-367 exam guide. Understanding integration points enables security engineers to establish end-to-end defense, streamline incident response, and enhance visibility across multiple layers of the network.
Integration also facilitates automation, central reporting, and correlation of alerts from diverse sources. By connecting the ESA with a unified management platform, professionals can detect coordinated attacks faster, enforce consistent policies across systems, and reduce operational complexity. Knowledge of integration techniques ensures candidates are prepared for enterprise-level challenges in both exam scenarios and real operational environments.
Continuous Learning and Professional Development
The cybersecurity landscape is constantly evolving, requiring ongoing education to maintain expertise in email security. Professionals preparing for the SESA exam benefit from continuous learning strategies that include simulation labs, industry webinars, and supplementary certification programs like the 98-368 exam overview, which emphasize emerging threats, analytical reasoning, and adaptive security practices. Engaging in continuous development helps security engineers stay current with new malware techniques, advanced phishing methods, and updates to the ESA platform, maintaining operational effectiveness over time.
Beyond technical skills, continuous learning fosters strategic thinking and leadership abilities. Security professionals can anticipate emerging risks, propose system enhancements, and advise organizational leadership on best practices. By combining hands-on expertise with ongoing professional growth, candidates position themselves as trusted experts capable of both defending critical communication channels and guiding broader security initiatives.
Advanced Malware Detection Techniques
A critical component of Cisco ESA is the ability to detect and mitigate sophisticated malware threats. The appliance uses features like sandboxing, heuristic scanning, and dynamic file analysis to identify potentially harmful attachments. Candidates can deepen their understanding by reviewing similar approaches in other technical certification guides, such as the 98-375 exam preparation, which emphasizes system monitoring, malware detection, and proactive threat identification techniques. Studying these frameworks helps security professionals develop the analytical mindset required to configure and optimize detection mechanisms effectively.
Integrating these malware defenses into operational workflows allows organizations to respond faster to zero-day attacks or coordinated phishing campaigns. By simulating attacks in a lab environment, candidates gain hands-on experience in configuring detection rules, interpreting alert outputs, and adjusting policies to minimize false positives. Mastery of these techniques is essential not only for exam readiness but also for ensuring enterprise resilience against evolving cyber threats.
Threat Intelligence Integration
Modern email security depends on actionable threat intelligence. Cisco ESA can integrate real-time feeds from external threat sources to dynamically block suspicious emails. Understanding the practical applications of threat intelligence is reinforced by studying exams like the 98-382 exam certification guide, which outlines approaches for leveraging external data to enhance security workflows. Candidates learn to interpret intelligence reports, correlate data points, and create automated policies that prevent attacks before they reach end users.
Effective integration of threat intelligence improves incident response times, enhances detection accuracy, and reduces the likelihood of system compromise. Candidates who understand how to implement these integrations are better equipped to design proactive security strategies. They can also provide actionable insights to management, demonstrating the value of intelligence-driven security in enterprise operations.
Content Filtering and Policy Management
Content policies in Cisco ESA are used to analyze message headers, body text, attachments, and embedded URLs for malicious or inappropriate content. Effective policy management ensures that legitimate communication flows uninterrupted while threats are mitigated. Security professionals can expand their knowledge by consulting guides like the 98-383 exam study materials, which detail structured approaches to content filtering, policy layering, and decision-making frameworks. These exercises help candidates develop precise, consistent rules that protect organizational email without causing unnecessary disruptions.
Candidates also learn to balance strict security enforcement with operational efficiency, applying policy prioritization techniques and exception rules where necessary. Practical simulations of content filtering allow security engineers to test policy effectiveness and adjust rules to align with organizational risk tolerance, ensuring that security strategies are both robust and adaptable.
Cloud Email Security Integration
The increasing use of cloud-based email systems requires understanding integration strategies between Cisco ESA and cloud services. Configuring secure connections, synchronizing policies, and monitoring cloud-based traffic are essential skills. Candidates often reference materials such as the 98-388 exam certification guide, which illustrates cloud system management principles and practical integration techniques. These insights help professionals ensure consistent security measures across on-premises and cloud environments.
Cloud integration also involves evaluating performance and reliability implications of routing email through cloud services. By applying lessons from other certifications, candidates develop strategies for maintaining security controls while leveraging cloud scalability and flexibility. This knowledge ensures seamless operation of enterprise email systems regardless of deployment model.
Encryption and Secure Communication
Encryption is a foundational component of secure email delivery. Candidates must understand how to configure Transport Layer Security (TLS), Secure/Multipurpose Internet Mail Extensions (S/MIME), and other encryption protocols within Cisco ESA. Exam preparation is often enhanced by consulting courses like the AI-102 certification guide, which, while focused on AI applications, also provides insight into securing communications and protecting sensitive data. Implementing encryption correctly helps organizations maintain confidentiality and compliance with regulatory requirements.
Proper encryption policies protect against interception, tampering, and unauthorized disclosure. Candidates also learn to configure encryption selectively, ensuring sensitive messages are encrypted without negatively affecting system performance or user experience. Mastery of encryption is a critical skill for both operational security and exam success.
Reporting, Analytics, and Metrics
Generating and interpreting reports is a critical skill for email security professionals. Cisco ESA provides comprehensive logs and reporting tools that track message flow, detect anomalies, and measure policy effectiveness. Candidates can enhance their analytical skills by studying frameworks such as the AI-900 exam preparation, which emphasizes data analysis, visualization, and decision-making principles applicable to security monitoring. Understanding these reporting tools enables professionals to identify patterns, optimize policies, and provide actionable metrics to stakeholders.
Analytics also support incident investigations, allowing teams to trace threats, assess vulnerabilities, and improve system configurations. Security professionals who can interpret reports effectively are better positioned to maintain operational efficiency and ensure continuous improvement of email security defenses.
Threat Response Automation
Automating threat responses is a key competency tested in the SESA exam. By leveraging Cisco ESA’s capabilities, security teams can automatically quarantine suspicious messages, block malicious senders, or trigger alerts for further investigation. Learning to implement automation workflows is reinforced through complementary exams such as the AZ-104 certification guide, which emphasizes infrastructure management, automation practices, and systematic troubleshooting. These skills allow candidates to create repeatable, efficient workflows that reduce response time and operational burden.
Automated responses also help maintain consistent enforcement of policies, ensuring that new threats are mitigated quickly and reliably. Candidates who master automation demonstrate an ability to align technical capabilities with strategic security objectives, enhancing organizational resilience against dynamic threats.
Advanced Policy Configuration
Beyond basic content and connection policies, advanced configurations enable granular control over message flow. Candidates learn to implement rules based on sender behavior, message characteristics, and user-defined criteria. Training materials like the AZ-120 exam preparation provide insight into complex configuration management and conditional rule application, which parallels advanced ESA policy design. This knowledge equips professionals to tailor policies for unique organizational needs while maintaining overall security posture.
Granular policy control also facilitates risk-based decision-making, allowing security teams to prioritize resources and protect critical communication channels. By combining advanced policy management with monitoring and analytics, candidates ensure that email security strategies are both adaptive and robust.
Incident Investigation and Forensics
Handling security incidents involves detailed investigation and forensic analysis of email traffic. Cisco ESA logs provide information on message delivery, sender behavior, and threat characteristics. Candidates often enhance their investigation skills using guides like the AZ-140 exam study materials, which emphasize system analysis, troubleshooting, and investigative workflows applicable across enterprise systems. Proficiency in incident investigation ensures that security teams can respond effectively to breaches and minimize operational impact.
Incident forensics also provides insights into emerging attack patterns, allowing teams to refine policies and improve detection capabilities. Candidates who practice forensic analysis gain the ability to reconstruct attacks, identify vulnerabilities, and implement targeted mitigation strategies, a skill set highly valued in enterprise security roles.
Cloud Infrastructure Security Integration
Cisco ESA increasingly operates alongside cloud infrastructure services, requiring professionals to understand security principles across hybrid environments. Effective integration ensures that both cloud-based and on-premises email systems adhere to the same security policies. Candidates benefit from learning approaches highlighted in certifications like the AZ-204 certification guide, which emphasizes secure application deployment and cloud security workflows. By understanding how to secure cloud email endpoints, candidates can maintain consistent defenses and operational continuity.
Cloud infrastructure integration also involves managing identity, access controls, and cross-platform policy enforcement. Professionals who master these principles ensure that enterprise email systems remain resilient, regardless of deployment model, and are well-prepared for real-world challenges in hybrid and multi-cloud environments.
Continuous Learning and Future Trends
The field of email security is continuously evolving, driven by emerging threats, regulatory changes, and technological advancements. Security professionals preparing for the SESA exam benefit from ongoing engagement with new tools, techniques, and platforms. By combining hands-on practice with continuous learning, candidates ensure that they remain proficient in threat detection, policy management, and system integration. Staying current with industry trends, guided by structured certification programs, positions professionals for long-term success and operational effectiveness.
Continuous learning also fosters strategic insight, allowing candidates to anticipate new attack vectors and recommend system improvements. Mastery of evolving technologies ensures that professionals maintain both technical competence and organizational value, enhancing career growth and the security posture of the enterprises they serve.
Understanding Python for Security Automation
Automation is a key component in modern email security, and scripting languages like Python are essential for implementing repeatable processes. Candidates preparing for the SESA exam can enhance their automation skills by reviewing structured learning material, such as the 98-381 prep guide introduction to Python programming, which explains basic to intermediate Python concepts applicable to security tasks. Python scripting allows engineers to automate message scanning, log parsing, and policy enforcement, which improves efficiency and reduces the likelihood of human error.
Integrating Python into email security workflows also allows professionals to create custom monitoring tools, automate alert generation, and streamline reporting processes. Mastery of scripting empowers candidates to implement scalable solutions across enterprise environments, reinforcing their technical expertise while enhancing operational agility.
Data Analysis and Decision-Making
Effective email security relies on the ability to analyze data and make informed decisions. Understanding data management concepts, such as those outlined in the Microsoft Azure DP-203 exam guide, provides insight into structured data analysis, aggregation, and reporting methods. These skills are directly applicable to monitoring email flows, evaluating threat intelligence, and generating actionable metrics that inform security policies.
By applying data analysis techniques, security professionals can identify trends in email traffic, detect anomalies, and optimize policy configurations. Analytical reasoning ensures that decisions are grounded in evidence, supporting both operational effectiveness and exam readiness, as candidates learn to interpret logs, assess risk, and implement corrective measures systematically.
Virtual Networks and Secure Communication
Understanding the architecture of virtual networks is critical for configuring secure email systems, especially in hybrid or cloud environments. The Cisco ESA interacts with network components, requiring knowledge of subnetting, routing, and secure communication channels. Professionals can enhance this understanding through creating and managing virtual networks in Microsoft Azure, which detail network configuration, connectivity strategies, and security best practices. Knowledge of virtual networks ensures that email traffic is routed securely, reducing exposure to interception or tampering.
Integration of email security with network management also allows administrators to segment traffic, apply network-based policies, and monitor connections for suspicious activity. Candidates who understand these principles can implement holistic security strategies that combine network segmentation with email policy enforcement, improving overall organizational resilience.
Benefits of Certification for Career Advancement
Achieving technical certifications demonstrates proficiency and commitment to continuous learning. Security professionals preparing for the SESA exam can gain career advantages by aligning their skills with industry standards. Top reasons to become a Microsoft Certified Azure Administrator highlight how certification validates expertise, enhances employability, and opens opportunities for senior roles in IT and cybersecurity. Certifications also provide structured frameworks for learning complex concepts, ensuring candidates build both knowledge and confidence.
Certification benefits extend beyond technical recognition; they signal an ability to solve problems, implement best practices, and contribute strategically to organizational goals. By pursuing complementary certifications, professionals strengthen their credentials and broaden their understanding of integrated systems, which is essential in dynamic enterprise environments.
Security Operations and Incident Response
Proficiency in security operations is essential for managing incidents effectively. The SESA exam assesses a candidate’s ability to detect, respond, and remediate email-based threats. Learning strategies for incident response to ace the Microsoft SC-200 certification, provide practical guidance for monitoring alerts, analyzing suspicious activity, and initiating corrective actions. Mastery of these strategies ensures that email systems remain resilient against malware, phishing, and other threats.
Incident response also involves documenting events, coordinating with teams, and improving system configurations to prevent recurrence. By integrating operational procedures with automated defenses, professionals can reduce response times, enhance situational awareness, and maintain compliance with organizational and regulatory requirements.
Object-Oriented Programming and Security Applications
Object-oriented programming (OOP) principles are important for building maintainable and scalable security scripts or applications. Understanding concepts such as wrapper classes, encapsulation, and inheritance supports the creation of modular scripts for email automation and monitoring. Candidates can deepen their OOP knowledge using guides like introduction to wrapper classes, which explain practical applications in security and system management. By applying OOP principles, engineers can write reusable code, streamline automation workflows, and implement more sophisticated policy logic.
OOP also supports integration with external APIs and security tools, enabling candidates to automate complex tasks such as threat intelligence ingestion, reporting, and notification workflows. Mastery of programming concepts allows security professionals to adapt rapidly to evolving threat landscapes and implement advanced, maintainable solutions.
Data Management: Lakes vs Warehouses
Handling email and security-related data effectively requires understanding different storage and processing models. Candidates can learn from comparative studies like data lake vs data warehouse, which highlight the advantages and limitations of each approach. For example, data lakes are useful for storing raw logs and threat intelligence feeds, while data warehouses support structured analysis and reporting. This knowledge is critical when configuring reporting, analytics, and monitoring tools in email security environments.
By applying these principles, security professionals can design efficient data pipelines, optimize storage, and facilitate real-time analysis of email traffic. Effective data management ensures that policy adjustments and threat responses are based on accurate and comprehensive information.
Front-End Integration and User Interface Considerations
While email security is often backend-focused, understanding front-end technologies and user interaction can enhance deployment and user adoption. Professionals preparing for the SESA exam can benefit from tutorials like top Angular 6 features, which cover dynamic interface elements and responsive design. Knowledge of front-end frameworks can be applied to building custom dashboards, reporting tools, and alert systems, improving the usability of security platforms for administrators and end users.
Well-designed interfaces reduce the likelihood of user errors, facilitate rapid interpretation of security alerts, and enable efficient policy adjustments. Candidates who consider front-end integration alongside backend security achieve a more holistic understanding of enterprise email protection.
Layout and Visualization Techniques
Visualizing security data effectively is critical for decision-making. Email logs, alerts, and policy metrics are more actionable when presented clearly. Techniques such as centering elements and using layout frameworks, illustrated in center elements with Flexbox vertical and horizontal guide, can enhance dashboard design and report presentation. Candidates who integrate these design principles create more intuitive interfaces for monitoring email security, making it easier to identify trends, anomalies, and potential threats.
Visualization also supports training, reporting, and executive briefings. By presenting data clearly, security professionals ensure that insights are accessible to both technical teams and management, improving communication and operational decision-making.
JavaScript Event Handling for Security Tools
Email security automation and monitoring tools often leverage web-based dashboards, requiring proficiency in client-side scripting. Understanding JavaScript behavior, such as preventing default actions, helps developers build reliable, interactive interfaces. Candidates can study tutorials like preventing default behavior in JavaScript to implement robust input handling and event management in custom dashboards. Proper event handling ensures that scripts execute reliably, reducing errors and enhancing the accuracy of monitoring and alerting systems.
By mastering these techniques, security professionals can maintain responsive, reliable interfaces that improve operational oversight. Strong front-end scripting knowledge complements backend security expertise, creating cohesive and effective security platforms.
Artificial Intelligence in Email Security
Artificial intelligence is increasingly integrated into cybersecurity, improving the detection of phishing, malware, and other email-based threats. Professionals preparing for the SESA exam benefit from understanding AI concepts and their applications, which are well explained in AI unveiled what you need to know about artificial intelligence. AI can analyze message patterns, identify anomalies, and predict potential attacks, allowing email security systems to respond proactively and reduce manual intervention.
By leveraging AI insights, security engineers can create adaptive defenses that continuously learn from emerging threats. Candidates who understand these principles gain the ability to integrate intelligent monitoring, improve detection accuracy, and optimize policy configurations, enhancing both operational efficiency and organizational resilience.
Choosing the Right Cloud Provider
Email security increasingly interacts with cloud services, making provider selection critical for performance, security, and compliance. Professionals can gain guidance from comparative analyses such as which cloud provider to choose: Linode vs AWS, which detail features, security options, and scalability considerations. Understanding the differences between cloud platforms enables engineers to make informed decisions about hosting, backup, and hybrid deployments while maintaining security and operational continuity.
Cloud selection also affects policy integration, threat monitoring, and compliance adherence. By evaluating cloud capabilities strategically, security professionals ensure that email infrastructure remains robust, scalable, and compliant with organizational and regulatory standards.
AI Agents and Automation
AI agents are increasingly used to automate routine security tasks, such as spam detection, attachment scanning, and policy enforcement. Studying guides like AI agents uncovered helps candidates understand the practical applications of autonomous systems in threat management. Integrating AI agents with Cisco ESA allows organizations to streamline workflows, reduce response times, and maintain consistent enforcement of security policies.
Automation supported by AI agents also enables predictive threat mitigation, where systems learn from historical incidents to anticipate new attack patterns. Candidates who master these concepts develop advanced problem-solving capabilities, ensuring they can implement intelligent, adaptive defenses effectively.
Machine Learning for Threat Detection
Machine learning is transforming cybersecurity by enabling systems to detect patterns that may indicate malicious activity. Professionals preparing for the SESA exam can enhance their understanding through the power of AWS Certified Machine Learning Specialty, which highlights practical applications of machine learning in operational environments. Applying these principles to email security allows engineers to classify messages, identify phishing attempts, and block malware automatically.
Machine learning algorithms also support continuous improvement, adapting to evolving attack techniques. Candidates who integrate these capabilities with Cisco ESA demonstrate proficiency in advanced threat detection and predictive analytics, key competencies for both certification and enterprise security management.
Responsible AI Practices
While AI offers significant advantages, ethical implementation is critical. Security professionals must ensure transparency, fairness, and accountability when deploying AI-driven systems. Best practices for responsible and transparent generative AI development provides frameworks for auditing models, monitoring outcomes, and mitigating unintended consequences. Applying these principles to email security ensures that AI-driven policies and detection systems are reliable, unbiased, and aligned with organizational standards.
Responsible AI also fosters trust among stakeholders and reduces legal or regulatory risks. Candidates who incorporate these considerations demonstrate maturity and strategic foresight, essential qualities for senior security roles.
Governance, Risk, and Compliance Tools
Effective email security is closely tied to governance, risk management, and compliance (GRC). Professionals can enhance their understanding through the most effective GRC tools for streamlining your organization’s processes, which explain frameworks for policy enforcement, audit tracking, and risk assessment. Integrating GRC principles with Cisco ESA ensures that email systems comply with regulations, reduce operational risk, and provide verifiable security reporting.
Candidates who understand GRC integration are equipped to align technical controls with organizational policy objectives. This capability strengthens enterprise security posture while demonstrating the strategic value of security engineering beyond technical implementation.
Low-Code Platforms and Security Automation
Low-code platforms are becoming essential for rapid application development, including security workflow automation. Studying materials like why low-code platforms are application development helps candidates understand how to create automated security dashboards, alerting systems, and monitoring tools without extensive programming. Integrating low-code solutions with Cisco ESA enhances operational efficiency, enabling security teams to deploy scalable, repeatable processes quickly.
Low-code automation also supports flexibility in handling emerging threats. Candidates learn to build adaptable workflows that can respond dynamically to new email security risks, combining technical proficiency with practical deployment skills.
Splunk Integration for Monitoring
Monitoring and analytics are critical for maintaining secure email environments. Tools like Splunk provide real-time visualization, log correlation, and alerting capabilities. Guides such as the value of Splunk certification in 2025 highlight how analytics expertise enhances operational oversight. By integrating Splunk with Cisco ESA, professionals can track message flows, detect anomalies, and generate actionable insights for policy adjustments and incident response.
Effective Splunk integration also improves reporting for compliance audits and management dashboards. Candidates who master these techniques demonstrate advanced operational capabilities, bridging the gap between technical execution and strategic oversight.
Evaluating Certification ROI
Investing in certifications is a strategic career decision. Materials like is a Splunk certification, a good investment in 2025 provide guidance on the long-term benefits of certification, including career growth, increased earning potential, and enhanced credibility. Professionals who combine SESA expertise with complementary certifications position themselves as highly capable security engineers, qualified to manage critical enterprise systems and lead security initiatives.
Certification ROI extends beyond personal benefit; it reflects an organization’s ability to attract skilled professionals who can maintain operational integrity, implement best practices, and reduce risk exposure.
ServiceNow Integration for Security Workflows
Integrating email security with ServiceNow enables automated incident management, policy enforcement tracking, and cross-system alerts. Candidates can learn practical integration strategies from ServiceNow integration guide exploring the different integration methods. Effective integration streamlines communication between security tools, ensures timely incident response, and improves operational transparency for management.
ServiceNow integration also allows for automated ticketing, escalations, and audit trails, ensuring that all security activities are documented and actionable. Candidates who master this integration can design cohesive enterprise workflows that enhance both efficiency and accountability.
Conclusion
The Cisco 300‑720 SESA exam represents a pivotal milestone for security professionals seeking to specialize in enterprise email protection. Mastery of this certification demonstrates not only technical expertise but also the ability to integrate security measures seamlessly into complex organizational environments. In today’s digital landscape, email remains one of the most common attack vectors, making proficiency in detection, prevention, and response critical for safeguarding sensitive communication. Professionals who prepare thoroughly develop skills that extend beyond basic configuration, encompassing advanced threat analysis, automation, compliance, and strategic system integration.
A central theme in achieving success with Cisco SESA is the ability to implement proactive threat detection and mitigation strategies. Security professionals must understand how to identify phishing campaigns, malware-laden attachments, and suspicious message patterns before they compromise organizational systems. This requires a combination of deep technical knowledge, hands-on configuration experience, and familiarity with advanced features like sandboxing, encryption, and dynamic policy enforcement. By mastering these capabilities, candidates are able to design layered defenses that minimize exposure and provide consistent protection across diverse enterprise environments.
Automation and intelligent system integration also play a crucial role in modern email security. Efficiently managing large-scale email systems demands the use of automation tools, scripting languages, and integration with threat intelligence feeds. Professionals capable of leveraging automation can streamline repetitive tasks, enforce policies consistently, and respond rapidly to emerging threats. Equally important is the integration of email security solutions with broader IT ecosystems, including cloud platforms, network monitoring tools, and incident management systems. This holistic approach ensures that security measures are coherent, scalable, and aligned with organizational objectives.
Compliance and governance form another critical aspect of email security operations. Enterprises must adhere to regulatory requirements while maintaining operational efficiency. Effective implementation of retention policies, audit tracking, and reporting mechanisms ensures that organizations remain compliant without compromising communication workflows. Security professionals who understand these requirements can design systems that not only meet regulatory obligations but also provide actionable insights for risk management and decision-making.
Finally, the value of continuous learning and professional development cannot be overstated. The field of cybersecurity is constantly evolving, with new threats, technologies, and frameworks emerging at an accelerated pace. Candidates who cultivate a mindset of lifelong learning, engage with emerging technologies, and expand their expertise in complementary domains are better equipped to adapt to change and drive operational excellence. By combining hands-on experience with strategic knowledge, security professionals can confidently implement robust defenses, optimize organizational processes, and position themselves as trusted experts within their organizations.